Definition
DevSecOps tools enable teams to integrate comprehensive security across the software supply chain, encompassing infrastructure, compliance, and operations, with AppSec serving as a foundational pillar.
What Are DevSecOps Tools?
DevSecOps tools transform security from a final deployment bottleneck into a continuous, automated mechanism embedded directly within the DevOps pipeline. Because DevSecOps has a broader scope than application code alone—encompassing infrastructure security, compliance automation, and operational security practices—these tools must secure multiple layers of the software supply chain.
Within this comprehensive approach, Application Security (AppSec) serves as a key pillar. By extending standard workflows with specialized AppSec capabilities, such as vulnerability scanning, policy enforcement, and artifact integrity checks, DevSecOps tools secure the delivery lifecycle without degrading release velocity.
No single tool covers all of DevSecOps. The discipline requires a coordinated ecosystem of capabilities that act proactively on source code, infrastructure configurations, dependencies, and binaries the moment they are created or modified.
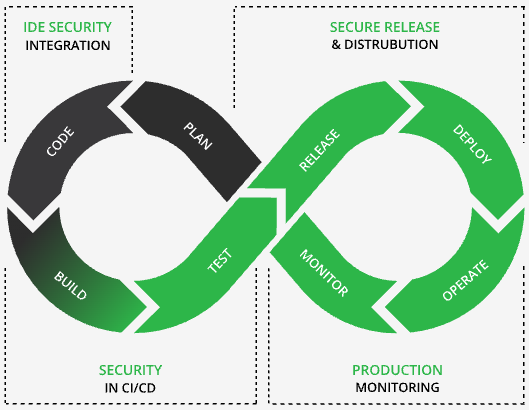
How do DevSecOps Tools Map to the SDLC?
Mapping a DevSecOps framework to the Software development lifecycle (SDLC) ensures that AppSec testing and policy enforcement occur contextually as code progresses from the developer’s workstation to the production environment. This lifecycle-aligned strategy relies on distinct categories of tooling tailored for planning, building, testing, deploying, and observing software.
Plan
During the initial phases of development, security requirements must be codified alongside functional requirements.
- Threat modeling identifies potential threats, attack vectors, and trust boundaries before any code is written. Teams work to surface design-level risks early and translate findings into security requirements and architecture decisions.
- Security requirements tooling establishes baseline defenses by converting threat model outputs into concrete, testable acceptance criteria.
- Issue tracking systems with security workflow support ensure vulnerabilities are treated as standard development bugs.
- Policy-as-code frameworks define security standards programmatically before code is written, making compliance enforceable and auditable by default.
- Developer security training equips engineers to recognize and avoid common vulnerabilities through role-based instruction.
- Secure coding standards provide guidelines tailored to specific languages and platforms that reduce inconsistency and establish a measurable baseline for code review and audits.
Build
As source code is compiled and dependencies are resolved, the toolchain must validate the integrity and safety of all inputs.
- Software Composition Analysis (SCA) scans open-source dependencies for known CVEs and license risks.
- Static Application Security Testing (SAST) analyzes proprietary code for vulnerabilities before execution.
- Software Artifact management and binary repositories store, version, and govern build outputs, ensuring clean builds through clean inputs.
- Secrets detection tools scan source code and build inputs for hardcoded credentials and tokens, preventing them from being compiled into build artifacts or propagated downstream.
Test
Testing verifies that compiled applications and their execution environments are resistant to active exploits.
- Dynamic Application Security Testing (DAST) tests running applications for exploitable vulnerabilities by simulating attacker behavior.
- Container image scanning inspects containerized environments for OS-level and dependency vulnerabilities.
- Software supply chain security tools scan artifacts, dependencies, and container images for malicious packages and integrity violations (e.g., JFrog Xray).
- Software Bill of Materials (SBOM) generation tools produce a comprehensive software bill of materials for every build, documenting all components.
Deploy
Deployment mechanisms must act as rigid security gates that prevent non-compliant software from reaching production.
- Policy enforcement gates block the promotion of artifacts that fail predefined security checks.
- Infrastructure-as-code (IaC) scanning validates cloud and infrastructure configurations prior to deployment.
- Artifact promotion tools enforce deployment gates between development, staging, and production environments by requiring cryptographic signatures before promoting artifacts between environments.
- Secrets management platforms inject credentials dynamically at runtime rather than during the build process.
Observe
Post-deployment, continuous monitoring is required to identify zero-day threats and operational anomalies in live environments.
- Runtime security monitoring detects anomalous or malicious behavior within production workloads.
- Runtime Software Bill of Materials (SBOM) reconciliation checks what is actually running in production against what was declared in the original SBOM to identify drift or unauthorized changes.
- Vulnerability management and prioritization tools continuously scan production environments against updated threat intelligence.
- Audit logging and compliance reporting maintain tamper-evident records to satisfy regulatory requirements.
- Incident response tooling enables engineers to trace a production issue backward through the supply chain to its original source.
What are key Terms in DevSecOps?
A well-architected DevSecOps platform relies on a specific taxonomy of tools, each addressing distinct Application Security vectors.
- IDE Integrated Tooling (Shift Left): Provides real-time security feedback directly within the developer’s Integrated Development Environment, catching vulnerabilities, risky dependencies, and hardcoded secrets as code is being written to genuinely shift security left.
- Software Composition Analysis (SCA): Identifies known vulnerabilities and license risks in open-source dependencies and third-party libraries, managing the “hidden” risks inherited from external code.
- Static Application Security Testing (SAST): Analyzes source code or binaries for security flaws without execution, enabling developers to catch and fix structural weaknesses early in the SDLC.
- Dynamic Application Security Testing (DAST): Evaluates a running application by simulating real-world attacks, catching runtime issues like configuration errors and injection flaws that static analysis can miss.
- Artifact Repository / Binary Management: The authoritative central store for all build outputs, enforcing immutability, access control, and traceability to ensure what is built is exactly what gets deployed.
- Supply Chain Security: Protects the entire build-to-deploy pipeline through artifact signing, SBOM attestation, and malicious package detection to verify every component is trusted and uncompromised.
- Container and Image Security: Scans Docker and OCI images for OS-level CVEs, misconfigured layers, and embedded secrets before deployment, securing the underlying infrastructure in microservices environments.
- AI/ML Model Security: Secures machine learning pipelines by scanning models and datasets for vulnerabilities, malicious code, and data poisoning, ensuring AI artifacts are governed with the same rigor as traditional software.
- Secrets Management: Centrally stores and injects sensitive credentials so they never appear as plain text in code or logs, defending against credential theft and accidental public exposure.
- Policy-as-Code / Admission Control: Programmatically enforces security standards through codified gates that cannot be bypassed, providing scalable compliance and blocking non-compliant artifacts from reaching production.
Where Artifact Management Fits
While active scanning and testing frequently dominate conversations surrounding DevSecOps tools, the artifact repository acts as the fundamental connective tissue of the entire toolchain. If the central store for build outputs is not secure, immutable, and strictly governed, all downstream security controls are inherently compromised.
Every tool in the AppSec pipeline interacts directly with artifacts. SCA scanners inspect them, SAST runs against their underlying source, DAST evaluates what they produce, and deployment gates manage their promotion. An ungoverned artifact store undermines every other security control, as mutable tags, unsigned binaries, and uncontrolled access create critical risks that traditional scanners cannot catch. A mature artifact management layer guarantees immutable storage, rigorous access control, cryptographic signing, SBOM attachment, and structured promotion workflows. Advanced supply chain security platforms build upon this foundation to provide continuous scanning, strict license policy enforcement, and malicious package detection across all artifact types.
Choosing DevSecOps Tools: What to Evaluate
Selecting the right components for a DevSecOps platform requires evaluating tools against strict technical criteria to ensure true risk reduction rather than superficial compliance. A practical evaluation framework prevents the adoption of siloed tools that generate alert fatigue or create a false sense of security.
- Pipeline Coverage: Verify if the tool addresses highest-risk phases or if it creates false confidence by scanning only a single isolated layer.
- Integration Depth: Determine if the tool plugs natively into your existing CI/CD systems, issue trackers, and artifact stores without necessitating significant custom engineering.
- Policy Enforcement: Assess whether the capability can automatically block bad artifacts and configurations, or if it is limited strictly to alerting.
- Supply Chain Visibility: Confirm that the tool allows you to trace a production artifact back through every discrete build step, dependency, and approval gate.
- Scalability: Ensure the tool performs reliably at the specific artifact and scan volumes your organization actively operates at.
- Compliance readiness: Check if the solution automatically generates the necessary audit artifacts, such as SBOMs, cryptographic attestations, and raw scan reports, required by your regulatory environment.
- Total Cost of Ownership (TCO): Reduce the financial and operational burden of tool sprawl by consolidating into a single, unified platform, cutting maintenance, integration, and licensing costs.
- Vendor and Community Support: Ensure long-term viability, continuous threat updates, and reliable troubleshooting by choosing tools backed by responsive vendors and robust community ecosystems.
Building a Cohesive DevSecOps Toolchain
Because no single tool covers the entirety of AppSec, organizations must architect a coordinated set of capabilities designed to minimize security blind spots and operational overlaps. The objective is a unified DevSecOps framework that provides seamless traceability and automated enforcement from code commit to production deployment.
Start with the artifact layer; a strictly governed binary repository forms the foundation that every other security tool relies upon. Ensure you instrument every phase of the pipeline, as coverage gaps in Plan, Build, Test, Deploy, or Observe create highly exploitable blind spots. Automate enforcement mechanisms wherever possible, because tools that merely alert without blocking create severe alert fatigue without tangibly reducing risk. Finally, build toward full traceability, keeping the end goal focused on a one-click trace from any production issue directly back to the specific commit, dependency, build, and approval that caused it.
JFrog DevSecOps Tools
DevSecOps tools are not an isolated checklist; they form an interconnected ecosystem that must operate cohesively across the full SDLC to effectively secure modern application delivery. By establishing a governed artifact repository as the foundational layer, organizations close critical supply chain gaps that attackers frequently exploit, maximizing the value of continuous scanning and testing.
Transitioning from fragmented security tools to a unified DevSecOps framework requires robust infrastructure capable of securing every binary, container, and dependency. The JFrog Platform empowers you with end-to-end visibility, security, and control for automating delivery of trusted releases.
JFrog DevSecOps tools include:
- JFrog Curation: Seamlessly curate software packages and ML Models
- JFrog Security Essentials (Xray): Integrated SCA for software and AI artifacts
- JFrog Advanced Security: Supply chain exposure, scanning, and impact analysis
- JFrog Runtime: Real-time visibility into runtime vulnerabilities
By providing immutable storage, continuous vulnerability scanning, and automated policy enforcement, JFrog ensures that only thoroughly verified, compliant software reaches your production environments.
To learn more about JFrog, book a demo or start a free trial.