helping to deliver secure software updates from code to the edge.
You have been redirected to the JFrog website
リソース
サポート&サービス
カスタマーサクセス
アカウントと信頼
AIの概要
エージェントの信頼性は、取り込み・生成・配布するものの信頼性によって決まります。JFrogは、すべてのAIモデル、Agent Skills、MCPサーバー、AI生成コード、そして生成されたアーティファクトを単一の信頼できる管理基盤(Single Source of Truth)で統制します。
エージェント型ソフトウェアサプライチェーン全体をセキュアに保護することで、新しい開発スピードでも信頼できるソフトウェアを提供できます。
JFrog AI製品
JFrog ML


JFrog ML
機械学習モデルとGenAIの構築、トレーニング、セキュリティ確保、デプロイ、提供、監視
JFrog AI Catalog
AIのエコシステムの検出、管理、保護
新しい機能
MCPレジストリ
エンタープライズ規模でのMCPのガバナンスとセキュリティ
エージェントスキルレジストリ
信頼できるAIエージェントのためのエンタープライズ統制スキル
エージェントAI
JFrogエージェントソリューション
モデルライフサイクル管理(MLOps)
データエンジニアリングと機能管理(DataOps)
AI/MLの開発と展開
MLSecOps
エージェント型の修復
一元化されたAI制御とガバナンス (JFrog AI Catalog)
JFrog AIエコシステム
ユースケース
AI/ML
DevSecOps
デバイス/IoT
クラウドソリューション
The JFrog Platform
信頼できるソフトウェアを、迅速に届ける
信頼できるリリースの提供を自動化するために、エンドツーエンドの可視性、セキュリティ、コントロールを提供する唯一のソフトウェアサプライチェーンプラットフォームですDevOps、DevSecOps、MLOpsの各チームを、単一の信頼できる情報基盤のもとに結びつけます
プラットフォームを表示
信頼できるリリースの提供を自動化するために、エンドツーエンドの可視性、セキュリティ、コントロールを提供する唯一のソフトウェアサプライチェーンプラットフォームですDevOps、DevSecOps、MLOpsの各チームを、単一の信頼できる情報基盤のもとに結びつけます
DevOps



JFrog Artifactory
ユニバーサルアーティファクトとMLモデルのリポジトリマネージャー
JFrog Distribution
利用拠点間での安全なソフトウェア配布
JFrog Connect
DevOpsの俊敏性を備えたIoTデバイス管理
DevSecOps




JFrog Curation
ソフトウェアパッケージとMLモデルをシームレスに選定・管理
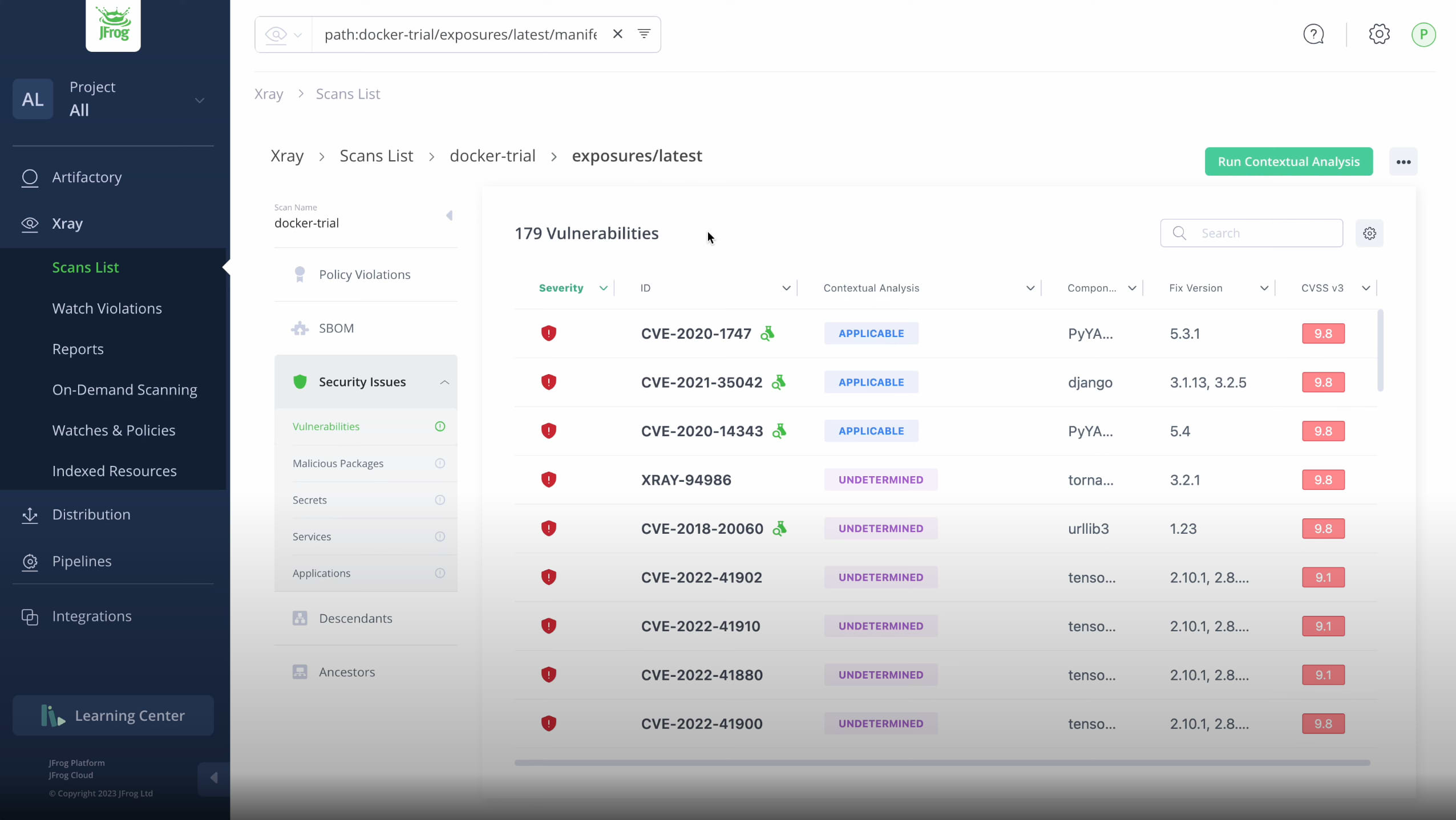
JFrog Security
Essentials (Xray) ソフトウェアとAIアーティファクトのための統合SCA
Essentials (Xray) ソフトウェアとAIアーティファクトのための統合SCA
JFrog Advanced Security
サプライチェーンのエクスポージャースキャンと影響分析
JFrog Runtime
ランタイム脆弱性のリアルタイム可視化
DevGovOps

JFrog AppTrust
アプリケーションリスクガバナンス
AI/ML


JFrog ML
AI/MLモデルの構築、トレーニング、運用、監視
JFrog AI Catalog
AIのエコシステムの検出、管理、保護
新しい機能
MCPレジストリ
エンタープライズ規模でのMCPのガバナンスとセキュリティ
エージェントスキルレジストリ
信頼できるAIエージェントのためのエンタープライズ統制スキル