How to Spend Less Time Fixing CVE’s
How much time and money can you save if you only focused on fixing what you need to… rather than simply “fixing everything?”
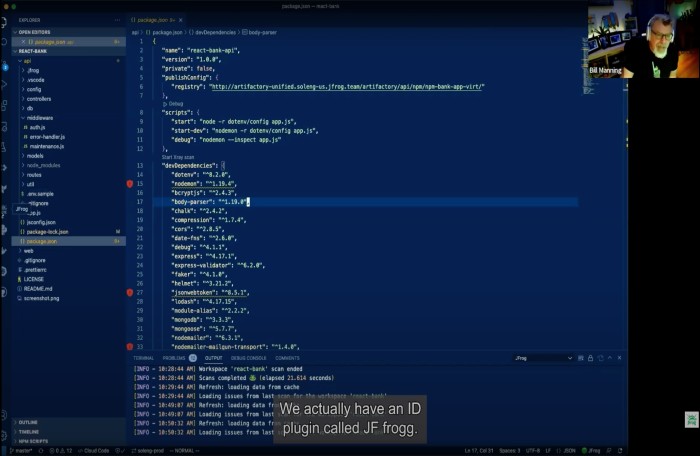
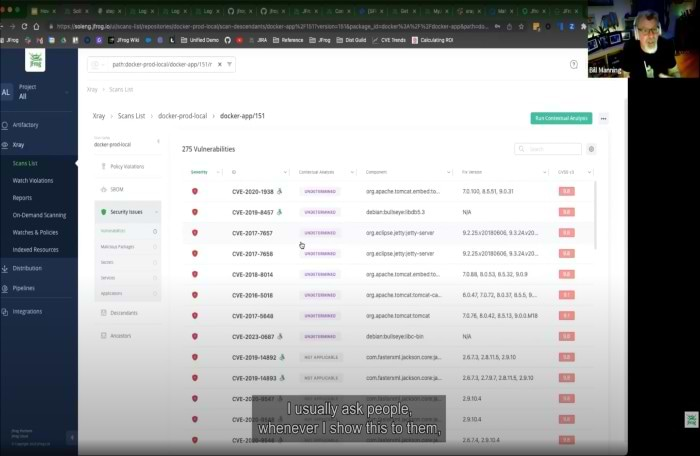
JFrog’s Contextual Analysis scans the container indicating whether a CVE is applicable (or not) to that specific container image. We provide concrete, and actionable remediation options that take into account relevance to your build, while providing proof points
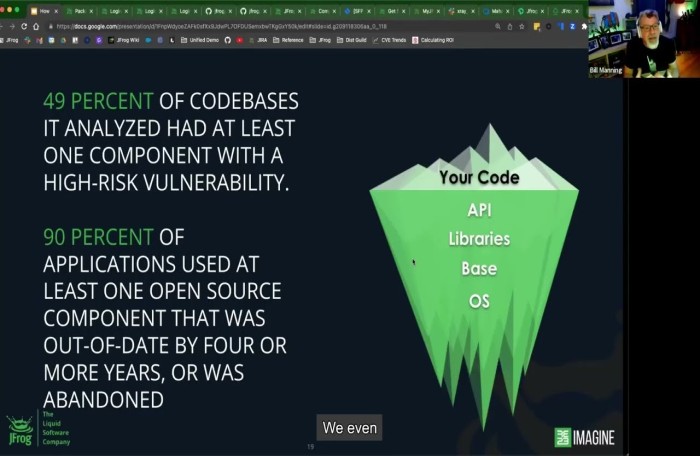
Let’s look a the four main risk areas of an open-source component
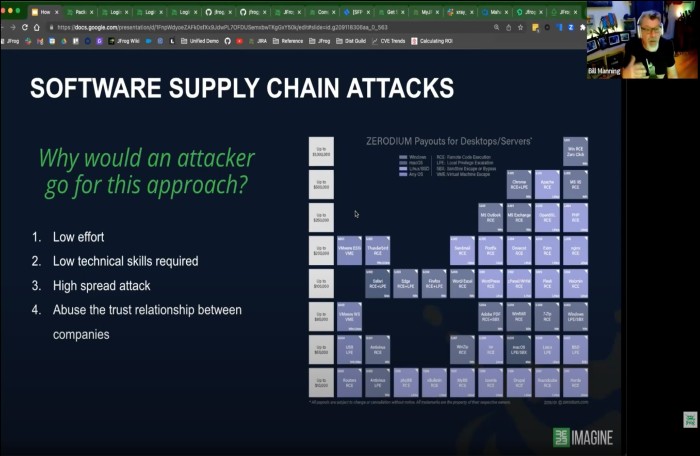
The four reasons that make your supply chain easy to penetrate and the cost of the damage in $ and time spent
Let’s look at the true cost of infinitely fixing vulnerabilities and a more modern approach to intelligently identify and fix vulnerabilities
Let’s look at a better system that intelligently identifies ONLY CVEs that are applicable to your software and IF they are worth your time remediating