Three Architectural Principles for Mythos & GPT-Cyber Readiness
How Organizations can Eliminate Cyber Kill Chain Risks Before the CVE Blitz Hits

Since Anthropic announced Project Glasswing and the capabilities of Claude Mythos Preview, and OpenAI announced GPT-Cyber – my calendar has looked the same every day: Back-to-back calls with CISOs, AppSec leads, and security architects. And every call starts with the same question:
“What do we need to do to prepare?”
It’s the right question. But the answer most people expect – a new tool, a new program, a new sprint to close gaps – misses something important.
Preparation for these new models isn’t additive. It’s structural.
The organizations most prepared for this new era of “Adversarial Symmetry” are not the ones with the most security scanners. It’s not even the ones with the most recent AI-security solutions. Rather, it is those organizations that have a single, authoritative system of record for every software artifact that moves through their environment. Those that are able to inherently secure and govern every aspect of their software from prompt to production, from any source, to any destination by integrating security and policy controls into their existing pipelines, not bolted on top.
Sounds far-fetched? Complicated? It’s actually straightforward. Let’s break it down.
What the New “Cyber Models” Actually Change
Let’s take Anthropic as an example. Anthropic’s Claude Mythos Preview found a 27-year-old vulnerability in OpenBSD, a 16-year-old bug in FFmpeg, and a 17-year-old remote code execution flaw in FreeBSD – all autonomously, without human guidance. It didn’t just find them. It built working exploits. And these are just a sneak peak into the many hundreds, possibly thousands, of zero-days that were already found.
Mythos is, as Anthropic themselves describe it, the first of many waves. Similar capabilities will proliferate to other frontier models, and eventually to open-weight models accessible to anyone. That means capabilities currently held by responsible actors conducting coordinated disclosure will eventually be available to those with no such constraints. This means an end-to-end security and governance problem which might not be new – but now it is dramatically accelerated.
The thing that reaches production was never just your code. It is an assembled binary: your code plus hundreds of open-source dependencies, transitive libraries, build tools, AI-generated components, MCP servers, and agent skills – many of which nobody explicitly reviewed or approved. That assembled artifact ends up being the attack surface. The new cyber models don’t inherently create vulnerabilities, they just find them faster. In turn agents can exploit them at a scale and speed no human team can match.
Organizations that wish to navigate this era must be structurally prepared.
Preparation Comes Down To Three Things
1. Govern within a single system of record. Managing all the artifacts that move through your organization – binaries, packages, builds, containers, AI models, releases – should happen in one place, one source of truth. When everything flows through one, system, you have full context, full software lineage, and the ability to apply policy at every stage automatically, without correlation across siloed tools.
2. Platform, not point tools. Security, governance, and AI control need to operate in the same management system mentioned above, connected at every stage of the artifact lifecycle. Tools bolted on after the fact don’t just slow you down, they create blind spots. In a Mythos-scale environment where exploitation windows are measured in hours, and attackers take advantage of the gaps between products, you need one cohesive trust layer that can tie binaries back to code repositories, and where detection, prioritization, remediation and governance happen in concert, not handed off between humans and siloed tools in sequence.
3. End-to-end control, from prompt to production. From the AI prompt that generates code to the production workload running it, every stage needs continuous, automated coverage at the scale of millions of artifacts and the speed of machine-driven triage. Not coverage you activate when you have time. Always on, at every gate, across your entire estate.
From Preparation to Practice – How a Defense Kill Chain Is Structured
1) The Foundation: A Single Source Of Truth
JFrog Artifactory provides you a foundational and structural position you can build around: Since Artifactory manages all binaries, dependencies, and metadata context by design (whether AI generated or not), the JFrog Platform can analyze, proactively respond, prioritize, suggest fixes, and govern at scale and with speed. Otherwise, how can you be expected to safely and completely govern what you don’t manage?
This infrastructure layer is what makes JFrog customers structurally better positioned for the “Cyber AI” era, compared to organizations cobbling together point solutions after the fact.
2) Platform Advantage – Closing the Loop at Machine Speed
The real question these new models pose is whether your entire approach to security can operate at a fundamentally different speed and scale.
Legacy security stacks were built for a slower world – a handful of critical CVEs per month, with weeks to triage, correlate, and remediate. That world is gone. When Mythos-class capabilities proliferate, organizations might find themselves facing hundreds of high-severity disclosures in rapid sequence, with exploitation windows measured in hours. You cannot solve this by moving faster through the same process. Accelerating manual, fragmented workflows doesn’t close the gap – it just fails more quickly.
The JFrog Platform is uniquely positioned to solve this: One platform that sees, manages and governs every artifact, enforces every policy, and connects every stage from ingestion to production – enabling workflows that close the loop on a critical CVE, from detection to blast radius mapping to validated release, at scale. It does so across multiple and transitive dependencies, it does so in whatever environment the customer chooses (On-prem, SaaS, Hybrid), it secures the AI-driven supply chain and it enforces trust.
3) The End to End Advantage
Preparation isn’t abstract. The JFrog Platform was designed and built to serve customers’ needs, especially in light of the disruptive changes in software development operations and security, brought on by the introduction of Frontier-Class Agentic Models, such as Mythos and GPT-Cyber.
Prevention: Before anything enters your environment, JFrog Curation acts as the policy-enforced gatekeeper. Malicious packages, packages with critical unresolved vulnerabilities, packages that violate your organizational policy are blocked at request, before a developer or agent can pull them. When a blocked version is requested, Curation automatically finds and serves the highest policy-compliant version available so that pipelines keep moving. Security isn’t the blocker.
Shift-Left Enforcement: JFrog Frogbot integrates security scanning and policy checks directly into the pull request workflow. Every PR is evaluated for new vulnerabilities, license violations, and policy gaps automatically, without requiring developers to leave their existing toolchain. The PR gate is a critical chokepoint: catching issues here, before they reach the build pipeline, costs a fraction of what remediation costs downstream. In a Mythos-scale environment where the volume of disclosures and the pace of development are both accelerating, keeping that gate automated and continuous isn’t optional.
Detection: The moment a CVE is disclosed, JFrog Xray’s Impact Search maps your blast radius instantly – every artifact across every repository that contains the affected package, its location, its last scan date, its path through your estate. The question “where are we exposed?” gets answered in seconds, not days of manual correlation across five tools.
JFrog does this across millions of artifacts, for organizations running thousands of developers across enterprise package ecosystems – from npm and Maven to PyPI, and Hugging Face models. Tools designed for a single ecosystem or a startup-scale repository cannot replicate this across a Fortune 100 scale environment.
For the cases where a dependency isn’t formally declared but copied directly into the codebase which is increasingly common with AI-generated code – JFrog Snippet Detection handles the hard problem that manifest-based scanners miss entirely: identifying reused code fragments, including altered or partially modified snippets, against a database of known vulnerabilities and license obligations.
Prioritization and Remediation: Before your team even starts triage, the JFrog Security Research team, powered by AI, has already done the hard work. Every CVE that surfaces is continuously enriched beyond raw CVSS scores: real-world exploitability analysis, identification of the specific vulnerable functions and the exact conditions required to trigger them, and remediation guidance that goes beyond “upgrade the package” – including deployment-level mitigations when a patch isn’t immediately available. This intelligence is embedded directly in the platform, triggering automated prioritization the moment a CVE is detected.
JFrog Catalog extends this further by acting as the proactive intelligence layer that monitors your entire software ecosystem for emerging risk, surfaces actionable recommendations at machine speed, and feeds that signal directly into your triage and remediation pipeline. For example, the difference between a CVSS 9.8 that is trivially exploitable and one that requires a configuration which no real organization runs is the difference between a P0 and a non-issue. JFrog makes that determination systematically and automatically, before your team is asked to act.
To confirm exposure in your specific binaries, Contextual Analysis determines whether a CVE is actually reachable in your code – not just present in a dependency, but executable in your artifact as built. Transitive Contextual Analysis extends this through indirect dependencies, tracing the full call chain so you know exactly where and how a vulnerability can be reached. The result: the list of CVEs your team needs to act on drops dramatically.
Finally, to help further prioritize CVEs in a Mythos-scale reality, JFrog Runtime helps narrow it down further by highlighting what’s actually running in production, and providing a clear view and remediation paths for unscanned or potentially risky artifacts.
Context-driven governance: Before a patched release reaches production, JFrog AppTrust provides you with the necessary business logic and application view. It enforces evidence-based stage gates across your release lifecycle. CVE policy rules run at every promotion point. Unresolved violations block progression. Every action is logged in an immutable audit trail, with signed attestations that make each release cryptographically verifiable. In a regulatory environment where the standard of reasonable defensive effort is shifting – that audit trail is not optional.
Across the AI supply chain: Mythos CVEs and zero-days are not limited to OSS packages only. Models, MCP servers, agent skills, external API calls your developers are making to services like OpenAI or Anthropic – JFrog AI Catalog governs what enters the organization, surfaces Shadow AI usage that exists outside approved workflows, and enforces policy before any component can be used in production. As agentic AI becomes standard in software development, this layer becomes as critical as package governance.
Prepare for the Next Wave, Not Only This One
Mythos and GPT Cyber are the first wave. Let’s be clear – they will not be the last. Comparable offensive capabilities will proliferate, and organizations that respond to each wave reactively will always be behind.
The preparation that matters is the one you do TODAY: establishing a single, governed system of record for your entire software supply chain; building security controls baked into every stage of the artifact lifecycle; and ensuring that when a new disclosure hits, you have the visibility, the triage capability, and the remediation pipeline to respond in hours, not weeks.
These models and the potential for what they can, and could do, changed the threat landscape fundamentally. The question is whether your security is fundamentally ready for this new AI-driven software supply chain security era.
Stay tuned for a part two of this blog – with more to come on governing and securing your software supply chain in the post-Mythos world. If you want to leverage the power of Mythos with the security of the JFrog Platform based on a single, authoritative system of record for every software artifact that moves through your environment, then feel free to take a tour, schedule a demo or start a free trial at your convenience.
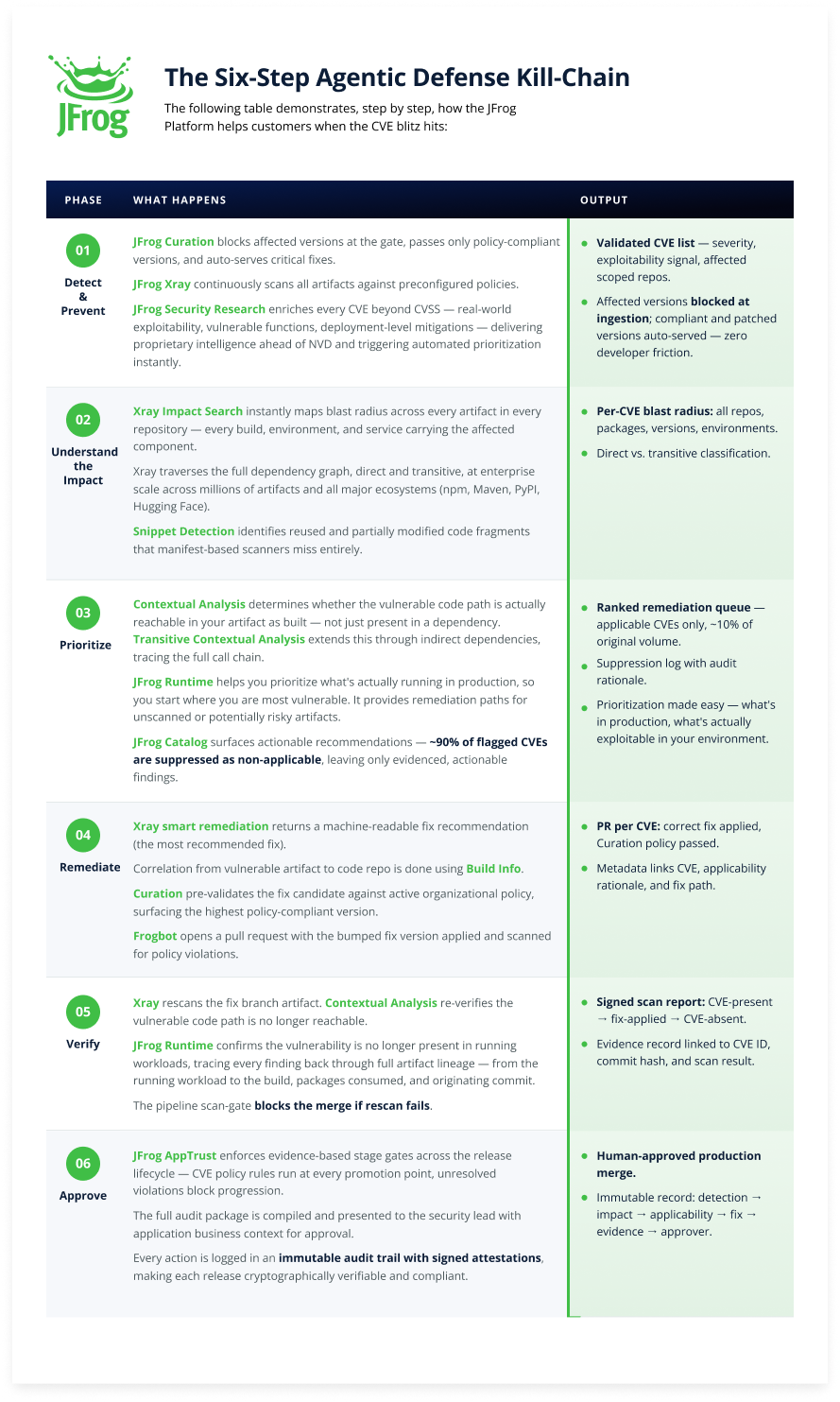
The Six-Step Agentic Defense Kill-Chain
The following table demonstrates, step by step, how the JFrog platform helps customers when the CVE blitz hits: