Governance That Ships: Embedding Policy as Code Into Your System of Record
Proving compliance is a necessity, but in a world of tightening regulations, the path to compliance is currently paved with spreadsheets, screenshots, and manual attestations.
We call this the “Audit Tax”, the millions of dollars and thousands of people hours spent not just integrating security, but on proving you are handling security.
With the advent of AI-assisted development, we now face a “tsunami of binaries” with increased risks, turning the traditional manual “compliance theater” into an existential risk. In a landscape of tightening regulations like the EU Cyber Resilience Act, failing to provide machine-speed proof of compliance no longer just causes delays; it leads to massive penalties of up to 2.5% of global revenue and the loss of the license to operate in key markets. You cannot scale development if your governance relies on human memory and Excel rows while your production volume is exploding and moving faster than ever.
Today’s market expects you to deliver continuous compliance at machine speed and prevent human-driven compliance drift. To achieve this, you need to codify your policies, i.e turn your policies into code that a computer can use. This approach is widely known as Policy as Code.
What is Policy as Code?
Policy as Code (PaC) is the practice of translating manual governance and compliance rules into machine-readable files that can be automatically enforced. By codifying your requirements (typically using the industry-standard Open Policy Agent (OPA) and its language, Rego) you transform static security standards into active, executable logic.
The following table compares the differences between traditional manual governance and the automated Policy as Code.
| Feature | Manual Governance | Policy as Code (PaC) |
| Flexibility | Rigid, closed-set policies | “Bring Your Own Policy” for precise control |
| Format | Subjective spreadsheets, screenshots, and attestations | Machine-readabale files (OPA/Rego) |
| Execution | Point-in-time, error prone, inconsistent, human-led reviews | Continuous, automated enforcement at machine speed |
The transition to an artifact-centric model provides a foundational layer of consistency. By moving away from point-in-time reviews, you ensure that your organization’s “rules of the road” are transparent and automatically enforced across every pipeline.
The Risks of Homegrown Governance Scripts
Many mature organizations have already adopted Policy as Code using the Open Policy Agent. However, we consistently hear the same industry-wide frustration: managing these policies as homegrown scripts in CI pipelines is incredibly brittle. The fundamental flaw is that DIY scripts validate the process, not the result, assuming that if a pipeline finishes, the code must be safe.
Relying on these homegrown implementations introduces several critical flaws to your software lifecycle:
- Point-in-Time Limitations: A pipeline check validates a process at a specific moment but it doesn’t secure the entire lifecycle, which many standards and regulations demand, such as the EU Cyber Resilience Act (CRA) or NIST SSDF. It just confirms the criteria specified in the Rego has been met.
- Visibility Gaps: If a developer bypasses the pipeline, detecting an unapproved package in production becomes nearly impossible. This blind spot is a massive liability. With Forrester reporting that 56% of external breaches result from application-related exploits, these unaccounted packages leave the door wide open for attackers.
- Metadata & Evidence Fragmentation: When governance is a DIY patchwork, critical metadata and attestations live in disconnected silos. This forces teams to manually “stitch together” the compliance story by chasing data across 10 or 15 different teams. Without a central system of record, this proof is often lost or stale by the time it’s needed, turning a routine audit into a multi-week investigation.
- Operational Burden: Maintaining custom, non-standardized scripts at scale creates a ‘Wild West’ environment that stalls innovation. Instead of building new features, highly skilled engineers get bogged down by an ongoing “audit tax,” forced to constantly debug, update, and patch fragile homegrown policies.
To close this gap, you need an enforcement engine that operates directly on immutable artifacts. JFrog AppTrust provides this by ensuring no unverified software reaches production, regardless of the path it took to get there.
The Solution: Automate PaC Inside Your System of Record
To navigate the tightening regulatory landscape, from NIST SSDF to the EU Cyber Resilience Act, governance must be more than abstracted logic. It requires a direct mapping to your software lifecycle.
We’re bringing native Policy as Code support within JFrog AppTrust to help organizations embrace DevGovOps, the practice of bringing governance directly into the DevOps environments developers already use. We know that many security and platform teams have already invested heavily in authoring OPA and Rego rules. Instead of forcing you to abandon that work or adopt a proprietary vendor language, AppTrust offers a “Bring Your Own Policy” (BYOP) model. You can now take the OPA and Rego policies you’ve already built and upload them directly into the JFrog Software Supply Chain Platform. This way, you natively enforce any custom governance rule to physically block non-compliant binaries and cryptographically prove compliance.
Accelerate Velocity with Evidence-Based Governance
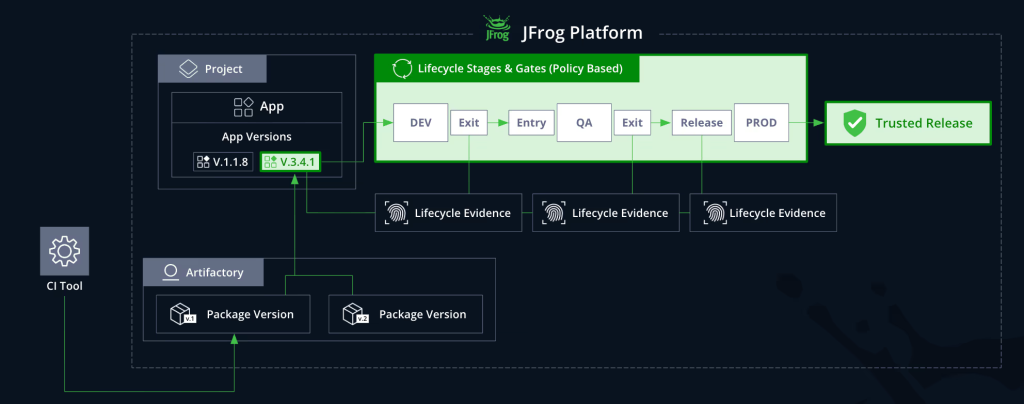
By combining the automated policy engine within JFrog AppTrust with JFrog Artifactory, you establish an active governance layer directly on top of your immutable System of Record. Transitioning to an artifact-centric Policy as Code model replaces manual guesswork with enforceable data. Utilizing JFrog as your System of Record yields several immediate benefits:
- Centralize Evidence: Stop chasing metadata across disconnected tools and teams. Consolidate all attestations into a single system of record, saving hundreds of hours otherwise spent on manual evidence collection.
- Bind Proof to the Binary: Link evidence, from GitHub reviews to ServiceNow approvals, directly to the artifact so it follows from build to production, preventing unverified code from ever reaching runtime.
- Ensure Verification: Create a cryptographically verifiable record for the entire software supply chain to provide the machine-speed proof required to meet strict regulations like the EU CRA and avoid significant non-compliance penalties.
You can finally eliminate the guesswork. Instead of hoping the process was followed, the artifact itself carries the evidence of its integrity. This unique combination ensures that your compliance rules aren’t just passive checks, but automated gates that protect the artifact at every stage of its journey.
Ready to eliminate the Audit Tax? Explore how native Policy as Code can secure your supply chain and book a demo today.