Webinar Recap: The Context Engine – Why Consolidation is the Natural Future of AppSec
As the software development lifecycle continues to evolve, the rise of AI is introducing both unprecedented productivity and unprecedented risk. In a recent webinar hosted by JFrog, Jens Eckels sat down with Forrester Senior Analyst Janet Worthington to discuss the state of application security (AppSec), the explosive growth of agentic software development, and why consolidating security tools is no longer a luxury, but a necessity.
Speakers:
- Jens Eckels – SVP, Global Communications, JFrog
- Janet Worthington – Senior Analyst, Forrester
Keep reading here for a detailed recap of their conversation, or watch the on-demand webinar.
The Evolution of AppSec and “Agentic” Software Development
Following introductions, Janet Worthington outlined how AppSec has radically changed over the last 12 to 18 months. Historically, AppSec teams have struggled with two major issues:
- Tool Sprawl: Shrinking budgets have forced companies to evaluate which tools to keep and which to cut, leading to confusion over overlapping functionalities.
- Vulnerability Backlogs: Massive backlogs of vulnerabilities require triaging, but AppSec teams have historically lacked the necessary “context” to know which vulnerabilities are actually critical.
However, the recent explosion of AI has shifted the landscape toward agentic software development. Today, AI agents are used throughout the entire software lifecycle—writing specs, code, documents, test cases, etc.
While this brings massive productivity gains, innovation, and speed, it introduces severe headaches for AppSec and Development leaders. They now have to worry about adoption, governance (who gets access to what), and—most importantly—quality and security. If an AI agent writes code, organizations must ensure it aligns with their style, avoids code bloat, doesn’t compromise reliability or performance. Critically, they must also prevent the introduction of unvetted vulnerabilities and insecure assets that often slip through when humans skip thorough reviews of machine-generated code. Ensuring these assets are maintainable and secure in the long term is now a primary challenge.
The Threat Landscape: External Attacks on the Supply Chain
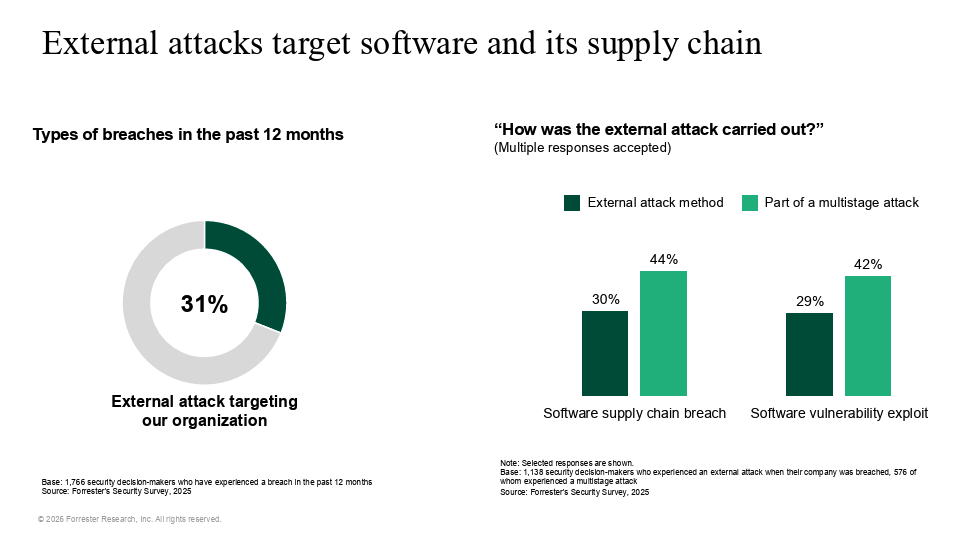
To contextualize the risk, Janet shared data from a recent Forrester survey of over 2,000 security decision-makers. When asked if their organization had been breached in the past year, 67% said yes.
When drilling down into how those breaches occurred:
- 31% were external attacks (not insider threats or employee mistakes).
- Of those external attacks, the two most common vectors were software supply chain breaches (30%) and software vulnerability exploits (29%).
Janet emphasized that these are often multi-stage attacks. Hackers aren’t just using one method; they are combining stolen credentials, SQL injections, software supply chain exploits, etc. to compromise systems.
The True Cost of a Breach
These attacks come with a massive price tag. According to Forrester’s data:
- The average cost of a general breach is $3.4 Million.
- However, if you suffer a software supply chain breach, that number jumps to $3.9 Million.
Why the premium? Supply chain breaches don’t just affect the target enterprise; they affect the enterprise’s customers, and those customers’ customers. A prime example is the Progress Software (MOVEit) breach. The fallout includes massive incident response efforts, residual costs, lost future revenue, unquantifiable brand damage, and class-action lawsuits.
The Toll on Developer Productivity
Beyond financial loss, these vulnerabilities place a heavy burden on developers. Developers are usually measured by “escapes to production” (defects that make it to the live environment) and Mean Time to Remediate (MTTR).
When a supply chain attack targets an open-source library, developers are forced to drop feature work to upgrade to a secure version. Sometimes, the secure version is several major releases ahead of what the team is currently using, resulting in breaking changes. Developers then have to rewrite their own code just to accommodate the patched library, destroying productivity.
The AI Code Tsunami
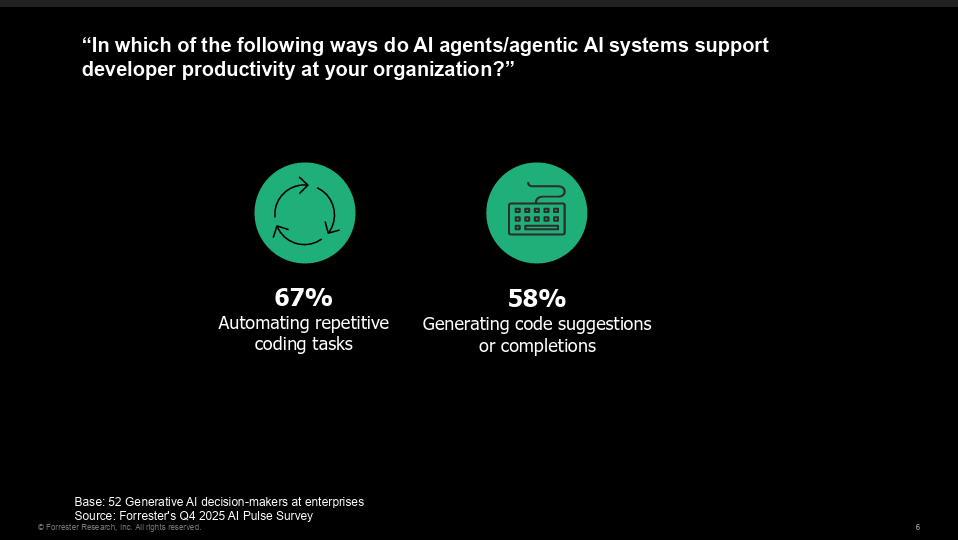
We can’t talk about modern development without talking about generative AI. According to Forrester’s Q4 2025 AI Pulse Survey:
- 67% of organizations use AI to automate repetitive coding tasks.
- 58% use it to generate code suggestions or completions.
Janet pointed out that industry leaders from Google to Microsoft are boasting that anywhere from 30% to 100% of their new code is written by AI agents. Cursor recently claimed that they are generating millions of lines of code daily, with just 3 developers.
But there is a catch: Code review is quietly becoming the bottleneck.
Humans are not doing line-by-line reviews of millions of lines of AI-generated code. As Janet noted, studies show that AI models struggle to write secure code from the start:
- Only 55% of generation tasks result in secure code (meaning 45% of the time, the model introduces a known security flaw).
- 22% of open-source models suggested or “hallucinated” non-existent package names, making them ripe targets for malicious actors to spoof.
The industry is learning that AI is not deterministic. Developers often assume the machine is “smarter than them” and skip thorough reviews, leading to a massive influx of insecure code hitting repositories.
Top Concerns with AI Adoption
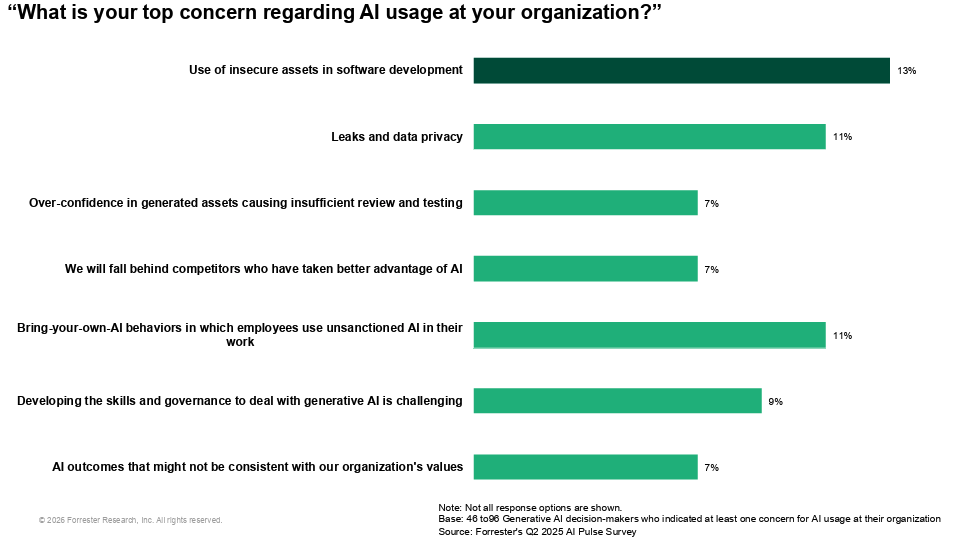
When Forrester asked AI decision-makers about their top concerns regarding AI usage, the results were telling:
- Use of insecure assets in software development (13%)
- Leaks and data privacy (11%)
- “Shadow AI” or bring-your-own-AI behaviors (11%)
- Over-confidence in generated assets causing insufficient review (7%)
These concerns reflect a reality where developers are pasting proprietary code into unsanctioned AI tools, or pulling in new, unvetted AI libraries (like LangChain) just to build new features, completely bypassing traditional security guardrails.
Adding AI to an Already Complex Supply Chain
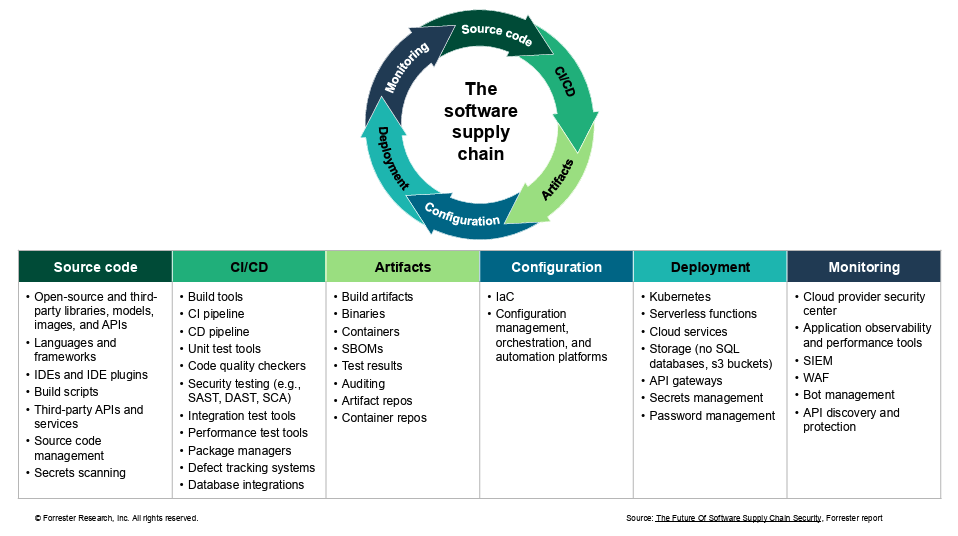
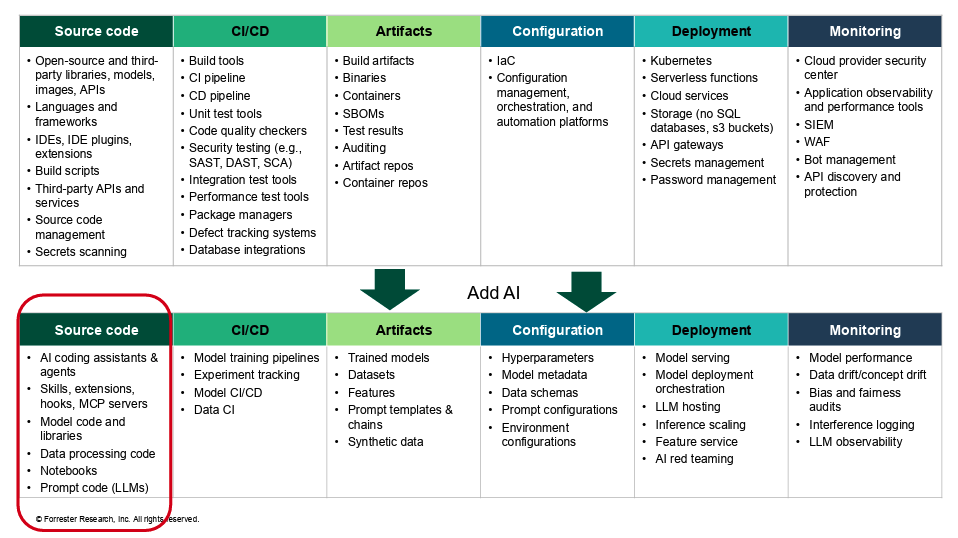
Before AI, the software supply chain was already overwhelmingly complex. It involved source code, CI/CD pipelines, artifacts, configuration, deployment, and monitoring.
Now, adding AI introduces an entirely new, parallel supply chain. Organizations have to secure AI coding assistants, model training pipelines, datasets, hyperparameters, model serving, and new dependencies. Janet noted that organizations are realizing they cannot manually manage this expanded attack surface.
The Shift Toward Security Consolidation
To combat this, the market is shifting. A few years ago, the vast majority of companies preferred a “best-of-breed” approach—buying the top standalone SAST tool, the top SCA tool, etc., and trying to wire them together.
Today, a Forrester survey reveals a perfectly split market:
- 43% prefer a holistic platform.
- 43% prefer best-of-breed tools.
- The remainder use a mix of both.
Janet explained that the shift toward platforms is driven by the need for context. Having 5 to 15 different security scanners alerting a developer is unmanageable. Organizations want a unified user interface, a shared underlying data model, simplified procurement, and cross-tool context so developers know exactly what to prioritize.
JFrog’s Approach: The “Bouncer” at the Club
Jens pivoted the conversation to JFrog solutions, specifically JFrog Curation.
Using a nightclub analogy, Jens described JFrog Curation as the “bouncer at the door.” Rather than letting a million open-source packages into the organization and scanning them later, JFrog Curation sits at the edge. It automatically blocks unapproved, insecure, unmaintained, or malicious packages (including AI models and MCP servers) from ever entering the developer’s environment.
This creates a “golden path” for developers. They are only allowed to pull from a pre-vetted, secure catalog of assets. This stops zero-day supply chain attacks before they happen and eliminates the cycle of developers building with bad code only to have it rejected by AppSec days later.
Jens then walked the audience through the complete end-to-end flow of the JFrog Software Supply Chain Platform, illustrating how context is maintained from the very first line of code all the way to the live production environment. By connecting what is curated on the left to what is running on the right, Jens explained that JFrog eliminates blind spots and provides the exact context both Security and Development teams need to operate safely at the speed of AI.
The Total Economic Impact (TEI) of JFrog
To prove the value of this consolidated approach, Jens shared the results of a commissioned Total Economic Impact (TEI) study conducted by Forrester Consulting in January 2026 on the JFrog Software Supply Chain Platform. The results included:
- 282% ROI
- Payback in under 6 months
- 38 hours saved per developer during onboarding
- 80% faster remediation of vulnerabilities
- $2.6M in increased productivity gains
- 71% reduction in development tool spend (due to consolidating legacy tools)
- 65% fewer vulnerabilities reaching production
Audience Q&A
The webinar concluded with two highly relevant audience questions:
Q: How do you manage the increasing workload of human reviews needed for the massive volume of AI-generated artifacts?
Janet: It definitely places a huge burden on human reviewers because of the sheer speed and volume of code being produced. The best way to manage this is by returning to the DevSecOps concept of “golden paths.” If you can ensure developers are put on a clean path from the start—meaning they are only allowed to build with pre-approved, secure libraries and are blocked from pulling in insecure packages—you eliminate the “low-hanging fruit.” By the time the code reaches a human for a final review, there is significantly less to review and fix.
Q: Will this new holistic approach from JFrog replace my existing legacy toolsets?
Jens: Customers are actively looking to consolidate and have been for a while now. Instead of maintaining separate SAST, DAST, SCA, and container security tools, which creates integration nightmares and alert fatigue, organizations are moving to unified platforms. The JFrog Platform is designed to replace those disjointed point solutions with a secure, governed, single source of truth, saving money and providing better, centralized context for teams.
Want more detail? Watch the full on-demand webinar.
Are you ready to consolidate your AppSec tools and prepare your supply chain for the AI era? Learn more about the JFrog Software Supply Chain Platform with a tour or free trial.