NIS2 Compliance in 2026: Compliance Doesn’t Have to Mean Complexity
Originally published February 2025 and updated March 2026.
The Network and Information Systems Directive 2 (NIS2) is the European Union’s effort to fortify cybersecurity across critical industries and services. Building on the original NIS Directive, NIS2 has broadened its scope, introduced stricter requirements, and placed greater emphasis on supply chain security.
As we move further into 2026, NIS2 has shifted from a looming directive to an active operational reality, with member states now enforcing their national laws. Furthermore, the regulatory landscape continues to evolve; just in January 2026, the European Commission proposed new amendments to streamline NIS2 and introduce standardized incident reporting. Today, organizations must focus on maintaining continuous compliance and integrating robust, automated cybersecurity measures into their operations.
At JFrog, we help organizations meet NIS2 compliance requirements by strengthening their security posture, securing their software supply chain, and ensuring they adhere to the directive’s cybersecurity and risk management standards.
What is NIS2?
Adopted in December 2022, the NIS2 Directive aims to establish a baseline for cybersecurity measures across the EU, as such, it applies to a wide range of organizations requiring well defined security measures to ensure European institutions are best protected from cyber attacks..
Key NIS2 Requirements
The NIS2 outlines key requirements to bolster security and resilience:
1. Data Security
Protect sensitive data through encryption, secure storage, and controlled access.
2. Quickly Detect and Respond to Cyber Incidents
Implement mechanisms for real-time monitoring and incident response to minimize impact.
3. Continuous Security Monitoring
Regularly assess systems to identify vulnerabilities and ensure compliance.
4. Analyze, Mitigate, Improve
Establish a process to analyze incidents, mitigate risks, and continuously improve security measures.
Who Needs to Comply?
The NIS2 Directive categorizes organizations into Essential Entities and Important Entities based on sector, size, and criticality. Generally, large and medium-sized organizations in specific industries fall under compliance requirements.
- Essential Entities
Organizations critical to the functioning of society and the economy, including:- Energy
- Transportation
- Healthcare
- Banking
- Important Entities
Entities integral to digital services and administrative operations, such as:- Digital Providers
- Public Administration
- Manufacturing
The January 2026 Proposed Scope Changes
To increase legal clarity and ease compliance burdens, the European Commission recently proposed updates to the scope of NIS2. Under these new proposals:
- New In-Scope Entities: Providers of European Digital Identity (EUDI) wallets and providers of strategic dual-use goods will be brought into scope, regardless of their size. Furthermore, all non-EU entities offering essential or important services within the EU will be required to appoint an EU-based representative.
- Exclusions & Adjustments: Small DNS providers will be excluded from the scope. The amendments also introduce a new “small mid-cap enterprise” category designed to lower compliance costs and ease supervisory pressure for thousands of companies.
The Push for Standardized Reporting
One of the biggest operational challenges of NIS2 has been the fragmented incident reporting processes. The newly proposed 2026 amendments aim to fix this by introducing a clear, standardized reporting procedure specifically for ransomware incidents.
Timeline for Compliance
Here are some key dates you need to know in terms of compliance requirements if you are located in or do business with the countries in the European Union:
| Date | Directive |
| December 2022 | NIS2 Directive adopted by the EU Parliament, emphasizing cybersecurity and operational resilience. |
| October 2024 | By this date, all EU countries were required to have adopted NIS2 regulations into their national standards. |
| January 2025 | By this date, it becomes mandatory for all EU organizations to demonstrate compliance, including robust cybersecurity measures, incident reporting, and supply chain risk management, by providing detailed information about software applications and their components. |
| January 2026 | The European Commission proposes targeted amendments to NIS2 to simplify jurisdictional rules, standardize ransomware reporting, and introduce the new “small mid-cap” category. |
How JFrog Can Help
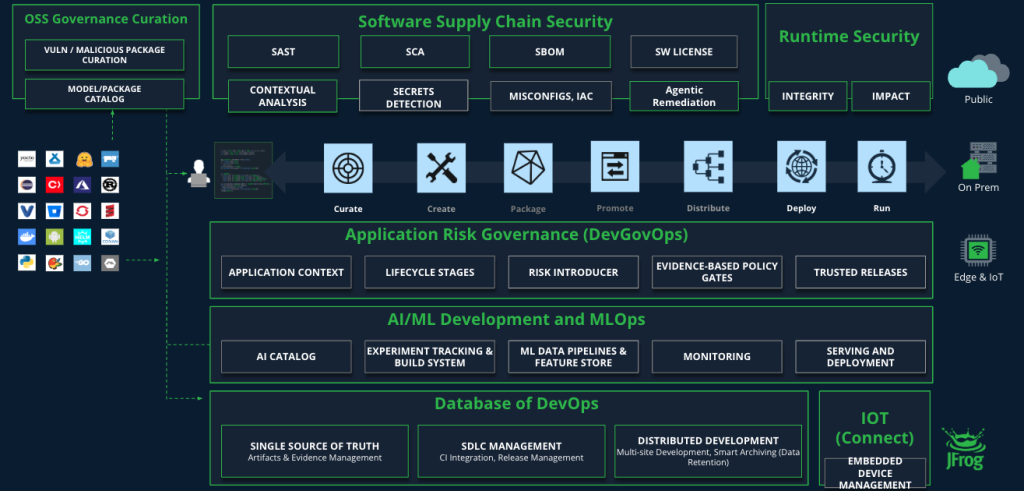
The JFrog Platform is designed to provide a unified, scalable, and secure approach to software management, ensuring that organizations can efficiently build, distribute, and secure their applications. By integrating automation, security, and compliance into every stage of the software development lifecycle, JFrog helps organizations protect their software supply chain, manage risk, and maintain regulatory compliance, including adherence to the requirements of the NIS2 Directive. To navigate these complexities proactively, organizations must adopt an automated governance approach.
Here are a few areas where the JFrog Platform can help:
1. Securing the software supply chain
- Advance Security Capabilities: Secure your software supply chain end-to-end by incorporating advanced tools such as contextual analysis, secret scanning, application and service misconfiguration detection, IaC vulnerability scanning, and SAST scans.
- Shifting Left: Identify security issues early in the development lifecycle by integrating security tools directly within developers’ IDEs, version control systems, and build tools.
- Curation: Automatically prevent malicious, vulnerable, and non-compliant open-source packages from entering your organization
- SBOM Generation: Automatically generate Software Bills of Materials (SBOMs) to provide the supply chain transparency and traceability that is explicitly mandated by European regulations.
2. Automating vulnerability management
- Real-Time Scanning: Continuously scans existing artifacts to identify newly discovered vulnerabilities after they enter the system.
- Contextual Prioritization: Focus on vulnerabilities with the highest impact, considering exploitability and usage.
3. Enhancing incident response and reporting
- Build Info & Traceability: Automatically collect metadata for every build and release, to monitor dependency, and artifact change in a structured format, enabling teams to trace security incidents back to the responsible team and affected software version.
- Alerting: Set custom policies and receive immediate notifications of violations to meet the 24-hour incident reporting requirement.
4. Ensuring integrity, resilience, and governance
- Release Lifecycle Management: Enforce environment based quality gates, customized through templates or Policy as Code (PaC) to act as a single point of control, so only validated artifacts progress through each stage. By automating approvals and providing compliance insights, you reduce risks, accelerate releases, and ensure final software integrity which are essential for any regulation.
- Automated Evidence Collection: Replace manual audit methods by generating machine-readable records of security, quality, and compliance checks. Ensure that only fully tested and verified releases are distributed, to meet NIS2 compliance requirements and promote greater confidence in the software supply chain.
- Runtime Security: Continuously verify application integrity in production by ensuring that only trusted artifacts are deployed from verified registries. Close windows of exposure with real-time visibility and advanced prioritization, aligning R&D, DevOps, and Security teams to quickly identify and mitigate vulnerabilities.
Why Choose JFrog?
Compliance doesn’t have to mean complexity. JFrog’s platform integrates seamlessly into your existing workflows, making it easier to:
- Streamline Compliance: Automate supply chain security and vulnerability management.
- Strengthen Cybersecurity Posture: Proactively address risks before they become incidents.
- Demonstrate Accountability: Provide auditors and regulators with clear, comprehensive evidence of compliance efforts.
Building a Resilient Future
As organizations enter 2026, software development operations must focus on complying with international standards and building resilient cybersecurity frameworks. Whether you’re located in the EU or doing business there, JFrog equips you to secure your supply chain, implement advanced security measures, and produce reports that document compliance with NIS2 and other emerging international standards.
For more information about how JFrog can keep you NIS2 compliant, feel free to take an online tour or schedule a one-on-one demo at your convenience.







