The State of the Software Supply Chain 2025
Managing and securing the software supply chain is crucial for trusted releases, but as any tech organization knows, it also presents significant challenges. With over 15 years of experience and a dedicated security research team, we at JFrog understand these threats. In a rapidly evolving post-AI world, DevSecOps teams are struggling to keep pace with changes.
To help address these challenges and prepare you for what’s to come, we’ve compiled a comprehensive report leveraging JFrog’s usage data, CVE analysis, and third-party polling data from 1,400 professionals. In this third annual Software Supply Chain State of the Union Report, we’ve incorporated more real-world data, increased survey respondents, and expanded our questions. The analysis offers insights into development trends, identifies risks, and explores securing your supply chain in 2025.
In this blog, I’ll give you a quick overview of some of our findings, including the latest software security trends. You can also download the full JFrog State of the Union Report here.
TL;DR top trends and insights
Four key themes emerged from our analysis:
- Your software supply chain is bigger, faster, and more complicated. Open-source ecosystem growth shows little sign of slowing down and organizations that are eager to innovate are moving fast to take advantage of the latest technologies.
- There’s more risk and more complexity than ever. While understanding the potential impact of a CVE continues to be a complex endeavor, it is just the tip of the risk iceberg.
- In addressing security risks, don’t skip the basics. Organizations have adopted varying levels of security frameworks and are using even more security tools, but some essential best practices are getting missed along the way.
- AI adoption is shifting into fifth gear. There are more options than ever for teams to bring AI services to production, but this presents new concerns for organizations to address.
In a nutshell, the software supply chain is rapidly evolving, and organizations are now exposed to new threats at an untenable pace. As the old adage goes, mitigating this increasing risk isn’t about working harder, but about working smarter. Simplifying toolchains and processes will be key for organizations aiming to move quickly, adopt new technologies, and stay ahead of the competition.
What is in your supply chain?
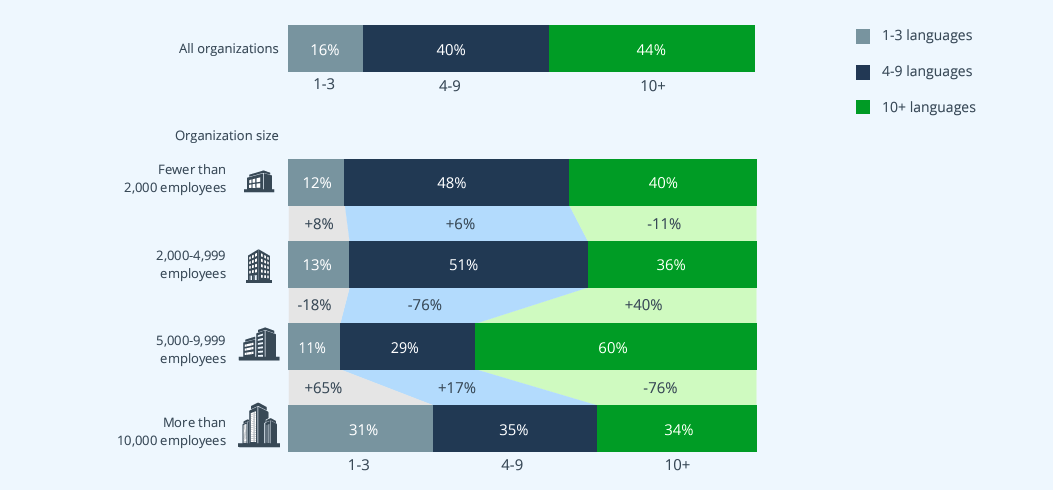
With two-thirds of organizations using 7 or more languages and nearly half using 10 or more, the risk for organizations exponentially increases since they now need to ensure that they have a consistent pipeline for multiple different languages, multiple different teams, and multiple different sources of threats. Each ecosystem has its own distinct vulnerabilities, malicious actors, and unique structures that must be taken into account during development to ensure the applications delivered to production are secure.
The state of software supply chain security
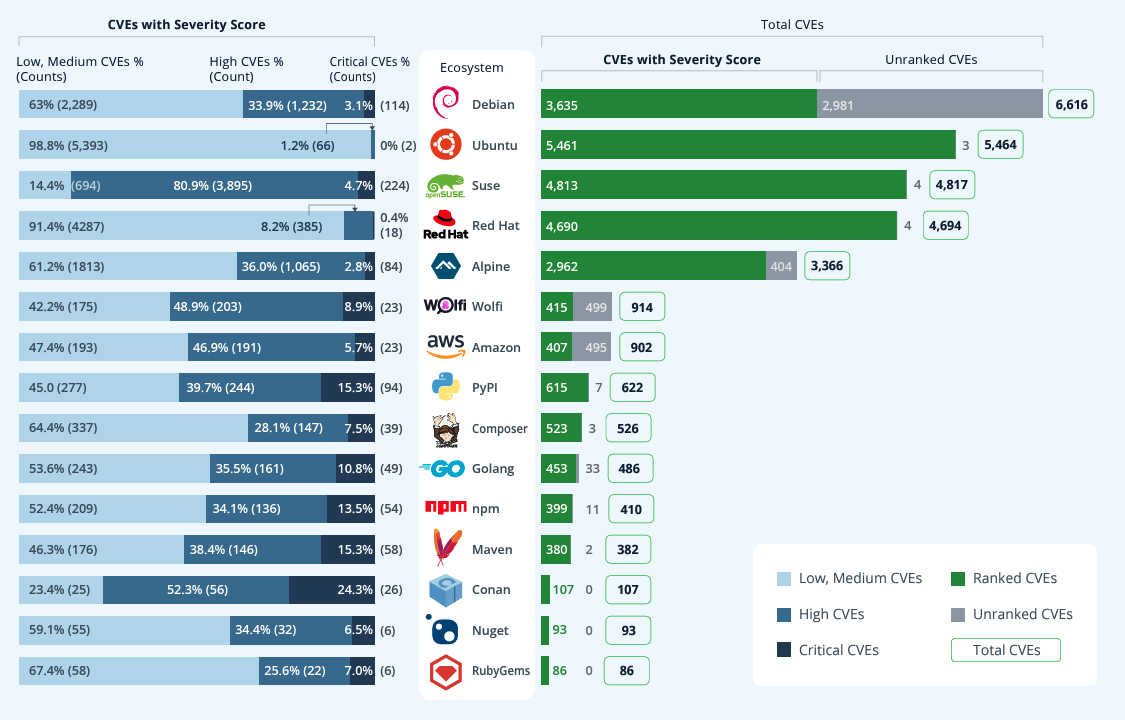
In 2024, security researchers around the world disclosed nearly 33,000 new CVEs, continuing the pattern of annual growth in CVEs discovered. While this is not surprising given the ever-increasing number of new open-source packages, the pace of CVE growth is surpassing the growth rate of packages, which is an indicator that should be taken seriously.
However, not all CVE ratings are what they seem. The CVSS ratings look purely at the severity of a successful exploitation of the vulnerability as opposed to how exploitable the vulnerability is. Sometimes, the configuration or method of exploit is a non-standard setting, making it very unlikely that the vulnerability will ever be exploitable. For example, based on a sample of 140 high profile CVEs, JFrog reduced the severity of Critical CVE scores 88% of time and High CVE scores 57% of time.This over-weighting of CVE scoring continues to be a concern year-over-year.
Preventing supply chain attacks
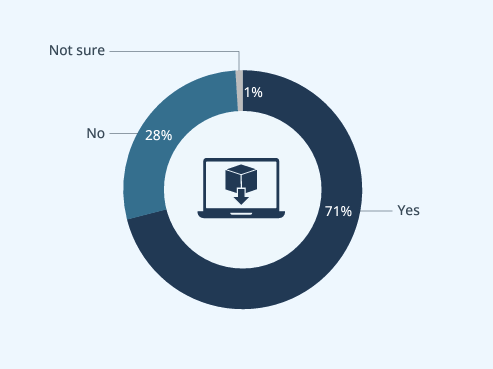
An alarming percentage of organizations allow their developers to download software components directly from public registries. Best practice is to restrict developers from downloading packages or libraries directly from the internet because the risk is simply too great, with the potential to expose an entire organization to attacks through a single developer’s machine. Traceability is also compromised, because there is no way to know what a developer is downloading if you allow them to download directly from the internet.
The fact that many organizations allow this indicates a need. An artifact management solution that proxies upstream public registries can be particularly useful. Acting as a central control point, it enables teams to track and secure every component in the software supply chain. This solution helps mitigate risks and prevent potential large-scale damage.
AI development is the next frontier of risk
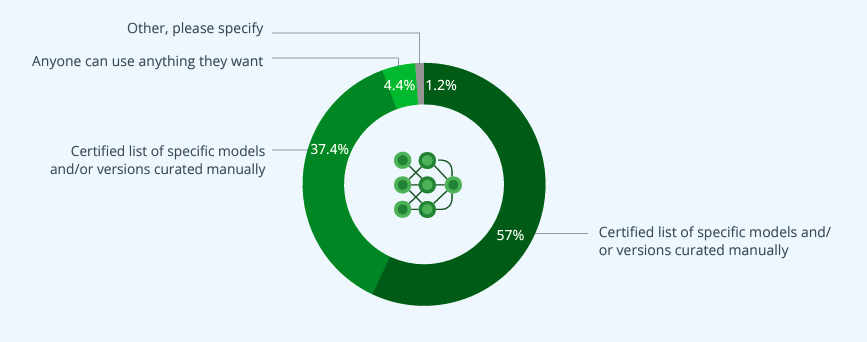
Many organizations struggle to establish reliable methods for managing the use of machine learning models within their applications, and they often lack a single source of truth for all software components, including ML models. Additionally, a significant blind spot exists in their ability to effectively track open-source packages that contain transitive dependencies related to ML models. When these critical gaps are present in the ML model development process, it not only becomes more challenging for organizations to manage their AI/ML supply chains efficiently, but also increases the risk of security vulnerabilities.
Wrapping up
I can’t emphasize this enough: the increasing complexity and pace of change within the software supply chain can heighten your organization’s risk more than ever. However, with the right tools, processes, and best practices, technical leaders can leverage the most diverse software ecosystem we’ve ever seen to cut through the noise and gain a competitive edge.
For the complete analysis—including our security findings, insights into the future of AI/ML, and practical security tips for protecting your software supply chain—read the full report. Also, stay tuned for the upcoming webinar where I’ll discuss the findings in real time.







