Boost Permissions Management with JFrog on Azure through Active Directory SSO
Editor’s Note (2024): Please refer to the current JFrog Software Supply Chain Platform listing on Azure Marketplace to get started with JFrog on Microsoft Azure.
When you’ve chosen Microsoft Azure to host your JFrog Cloud Enterprise or Enterprise+ subscription , you’ll naturally want to make good use of the services Azure provides for security and user administration.
DevOps security starts with who has access to your builds, releases, and automation. The JFrog DevOps Platform on Azure makes it easy to integrate with Azure Active Directory for managing user credentials as the first, unifying gate for secure permissions to your mission-critical development pipeline.
SSO and SAML
Organizations use many different software services to get work done, and maintaining individual credentials for each one becomes burdensome. Through Single Sign-On (SSO), administrators can grant each user individualized permissions to log into the set of services they’re authorized to use, while maintaining only one set of credentials for the entire enterprise.
One open standard for this purpose, Security Assertion Markup Language (SAML) enables an identity provider (IdP) such as Azure Active Directory to pass central authorization credentials to other services — including the JFrog DevOps Platform — for an SSO user experience.
The JFrog Platform supports SAML for SSO in JFrog Enterprise and Enterprise+ level subscriptions, and can integrate with Azure Active Directory for credentials management.
Setup for SSO
Integrating the JFrog Platform with Azure Active Directory for Single Sign On involves two easy procedures:
- Add JFrog Artifactory to your list of managed SaaS apps in Azure Active Directory.
- Configure SAML SSO in the JFrog Platform.
Microsoft has provided a detailed tutorial. In broad strokes, here’s what you will need to do for a SAML configuration.
Azure Portal
In the Azure Marketplace, get the JFrog Artifactory application integration to add your JFrog SaaS subscription.
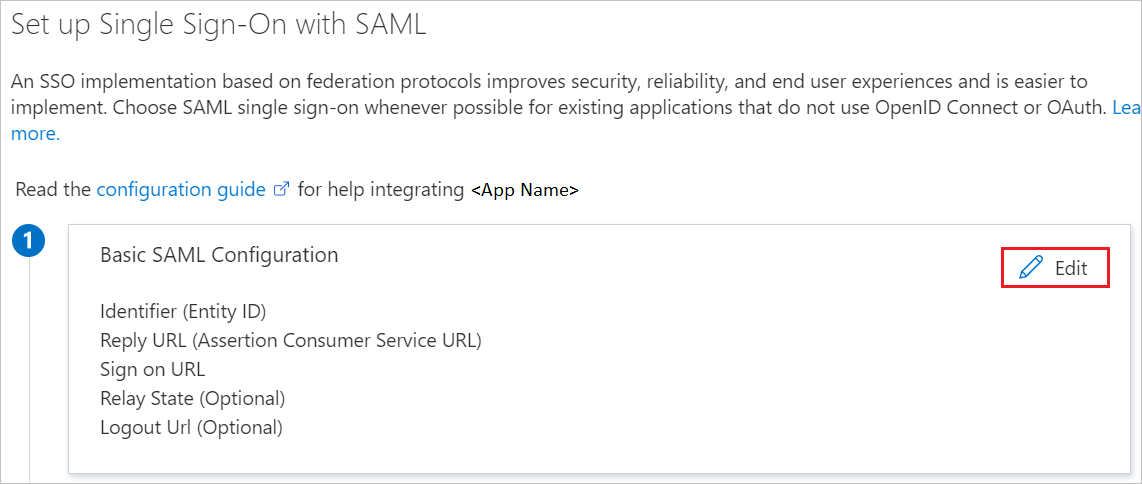
Edit the Basic SAML Configuration to configure the application in IDP and/or SP initiated mode(s).
For IDP Mode
In the Identifier text box, enter the domain of your JFrog Platform service:
<servername>.jfrog.io
In the Reply URL text box, enter the SAML URL for your JFrog Platform service:
https://<servername>.jfrog.io/artifactory/webapp/saml/loginResponse
For SP Mode
Click Set additional URLs
In the Sign-on URL text box, enter the login URL for your JFrog Platform service:
https://<servername>.jfrog.io/ui/login
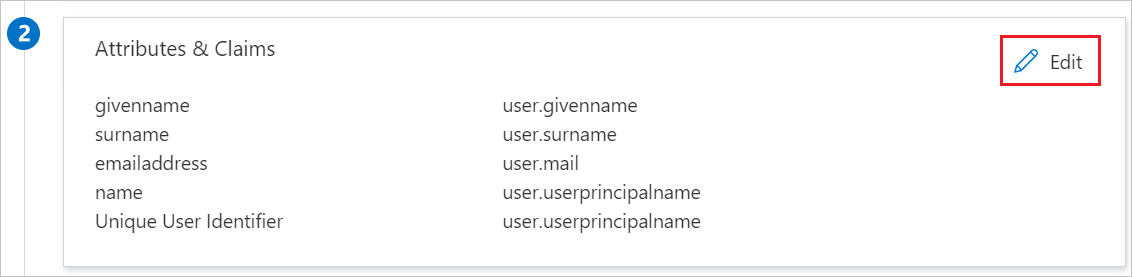
Edit the User Attributes to add custom mappings to your SAML token attributes configuration.
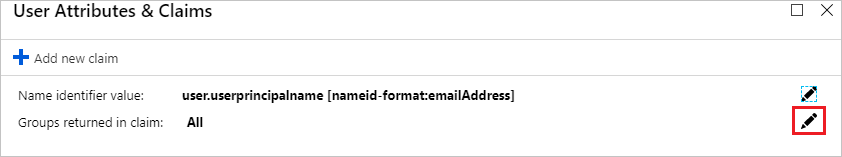
In the User Attributes & Claims section, add a new claim for all groups.
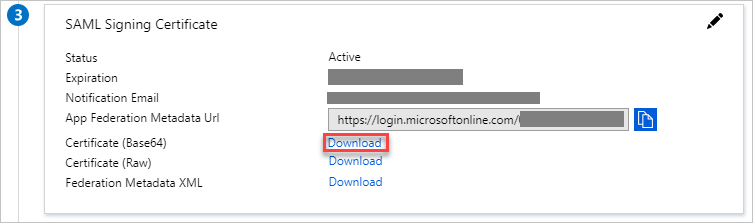
In the SAML Signing Certificate section, download the Base64 certificate. You will need this to configure SAML SSO in the JFrog Platform.
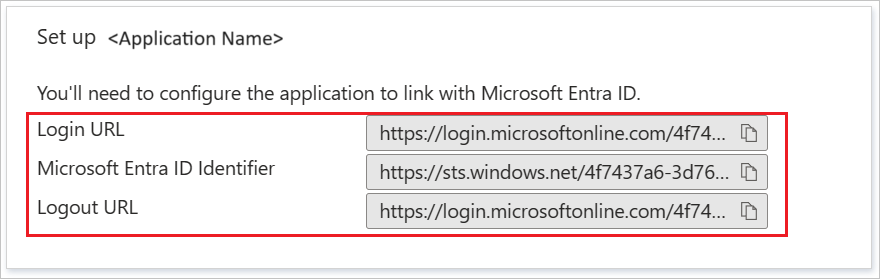
In the Set up JFrog Artifactory section, copy the provided URL(s). You will need these to configure SAML SSO in the JFrog Platform.
JFrog Setup
With Azure Active Directory configured, you can now configure JFrog Platform SAML SSO to work with it.
In the Administration module, go to Security | SAML SSO, enable SAML integration, and enter the needed information..
- Enter the SAML Login and Logout URLs that were provided to you in the Setup JFrog Artifactory section.
- For the SAML Service Provider Name, enter the base URL of your JFrog Platform service: <servername>.jfrog.io
- Enter the Base64 certificate provided to you in the SAML Signing Certificate section.
- Enter the user attributes for group and email.
- Select other options as shown and click Save.
Permissions Control
Once your teams have SSO access to the JFrog Platform, that’s only the start of your administrative control.
The JFrog Platform provides one-stop administration for your core DevOps resources. Through the same single pane of glass, administrators can set up permissions profiles for Artifactory repositories and builds, Distribution release bundles, and Pipelines CI/CD.
Once integrated with AAD identity management, administrators can assign those permissions profiles to user accounts, or to groups of accounts. This enables admins to limit individual users or groups to certain repositories and pipelines in Artifactory, for fine-grained control of access.
Blue Skies Ahead with JFrog on Azure
This is only one of the many ways your administration duties can benefit from an Azure-hosted JFrog Cloud Enterprise account, by leveraging the services of your chosen cloud provider.
You can purchase a JFrog Cloud Enterprise+ plan on Azure Marketplace This enables the convenience of using your organization’s established Azure account and existing Azure cloud credits.