Resources
Support & Services
Customer Success
Account & Trust
Community
Check out JFrog’s community, review expert resources, get latest community news, and more
Documentation
See the latest product documentation, research JFrog offerings and get answers on how to configure and use JFrog products
Integrations
Learn how to integrate JFrog products with 100+ providers such as ServiceNow, GitHub, NVIDIA, Sonar and more
Support
Open a ticket, get assistance or search for answers with JFrog Support and FAQs.
AI Overview
Your agents are only as trustworthy as what they consume, build, and ship. JFrog governs every AI model, agent skill, MCP server, AI-generated code, and assembled artifact in a single source of truth.
Secure your entire agentic software supply chain so you can ship trusted software at your new speed.
JFrog AI Products
JFrog ML


JFrog ML
Build, Train, Secure, Deploy, Serve and Monitor ML Models and GenAI
JFrog AI Catalog
Discover, Govern and Secure Your AI Ecosystem
New Capabilities
MCP Registry
MCP Governance and Security at Enterprise Scale
Agent Skills Registry
Enterprise governed skills for trusted AI agents
Agentic AI
JFrog Agentic Solutions
Model Lifecycle Management (MLOps)
Data Engineering & Feature Management (DataOps)
AI/ML Development and Deployment
MLSecOps
Agentic Remediation
Centralized AI Control & Governance (AI Catalog)
JFrog AI Ecosystems
JFrog AI Resources
Agentic Software Supply Chain Security: AI-Assisted Curation and Remediation
How to Detect and Eliminate Shadow AI in 5 Steps
Beyond Models: JFrog AI Catalog Evolves to Detect Shadow AI and Govern MCPs
AppTrust, AI Catalog, and more – Live product showcase from JFrog
MLOps Masterclass: Gain end-to-end control and governance over your AI/ML Workloads
From Chaos to Control: Future-Proof Your AI Supply Chain
See More Resources
Use Case
AI/ML
DevSecOps
Device/IoT
Cloud Solutions
Integrations
The JFrog Platform
Deliver Trusted Software with Speed
The only software supply chain platform to give you end-to-end visibility, security, and control for automating delivery of trusted releases. Bring together DevOps, DevSecOps and MLOps teams in a single source of truth.
View Platform
The only software supply chain platform to give you end-to-end visibility, security, and control for automating delivery of trusted releases. Bring together DevOps, DevSecOps and MLOps teams in a single source of truth.
DevOps



JFrog Artifactory
Universal Artifact & ML Model Repository Manager
JFrog Distribution
Secure Distribution Across Consumption Points
JFrog Connect
IoT Device Management with DevOps Agility
DevSecOps




JFrog Curation
Seamlessly Curate Software Packages & ML Models
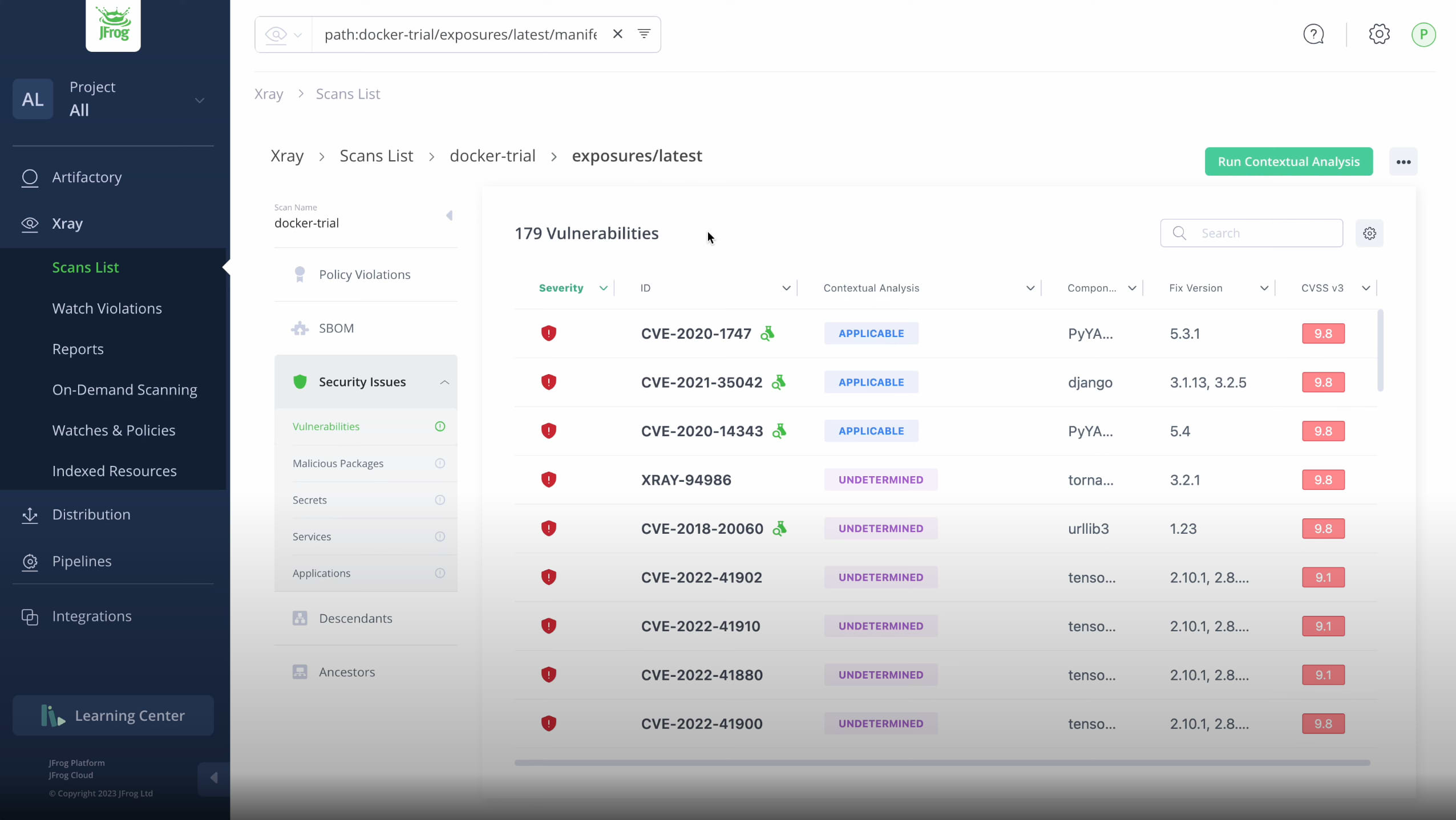
JFrog Security
Essentials (Xray) Integrated SCA for Software & AI Artifacts
Essentials (Xray) Integrated SCA for Software & AI Artifacts
JFrog Advanced Security
Supply Chain Exposure Scanning & Impact Analysis
JFrog Runtime
Real-time visibility into runtime vulnerabilities
AI/ML


JFrog ML
Build, Train, Serve and Monitor AI/ML Models
JFrog AI Catalog
Discover, Govern and Secure Your AI Ecosystem
New Capabilities
MCP Registry
MCP Governance and Security at Enterprise Scale
Agent Skills Registry
Enterprise governed skills for trusted AI agents
Use Case
Cloud Solutions
AI/ML
Platform Ecosystem
Deliver Trusted Software with Speed
The only software supply chain platform to give you end-to-end visibility, security, and control for automating delivery of trusted releases. Bring together DevOps, DevSecOps and MLOps teams in a single source of truth.
View Platform
The only software supply chain platform to give you end-to-end visibility, security, and control for automating delivery of trusted releases. Bring together DevOps, DevSecOps and MLOps teams in a single source of truth.
DevOps



JFrog Artifactory
Universal Artifact & ML Model Repository Manager
JFrog Distribution
Secure Distribution Across Consumption Points
JFrog Connect
IoT Device Management with DevOps Agility