JFrog & GitHub: Accelerating Secure Software Development Workflows
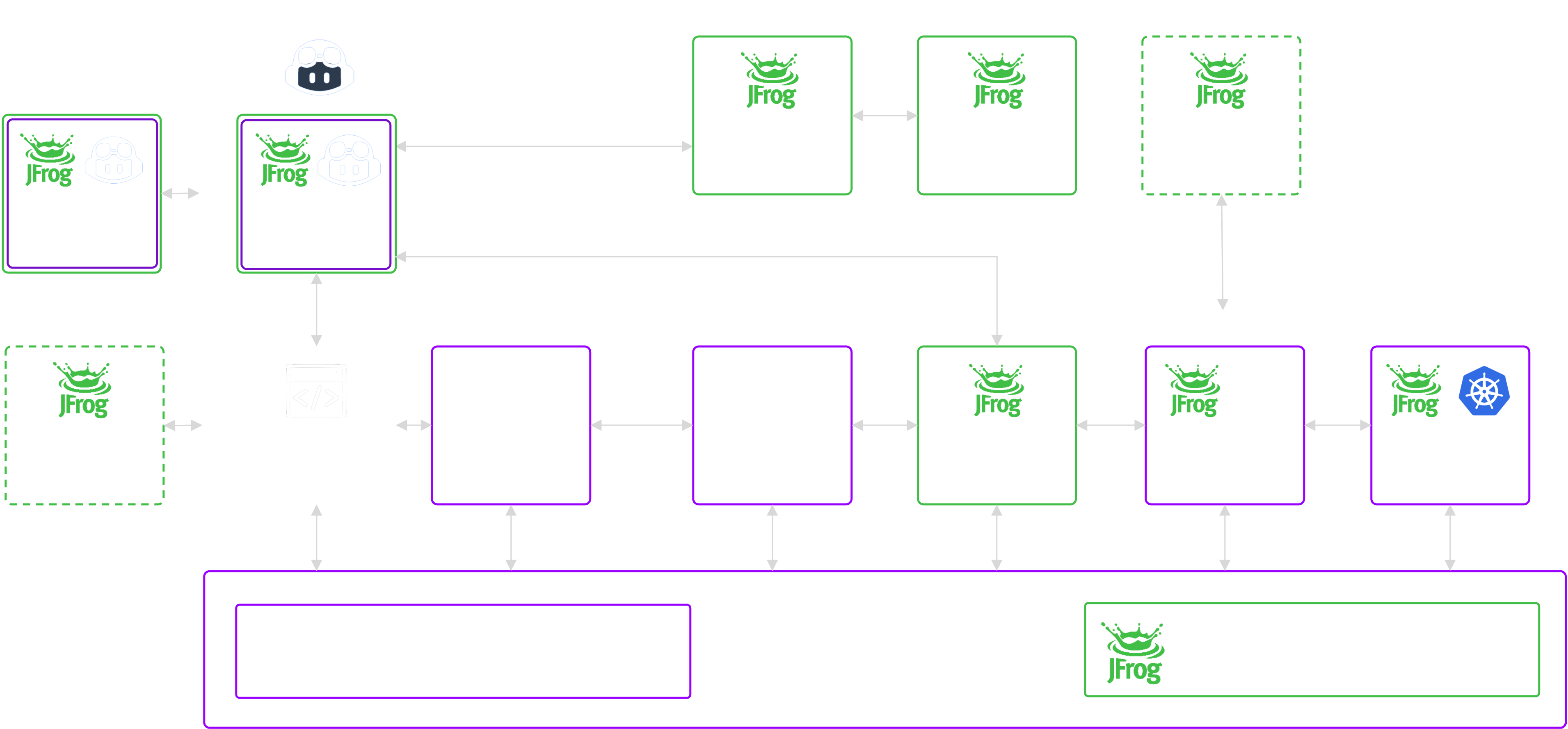
Creating secure workflows with best-of-breed code & binary-centric platforms for a unified and seamless experience across the software
supply chain.
The Power of GitHub and The JFrog Platform
What Customers Think of the GitHub Integration
AT&T
Morgan Stanley
Fidelity
Vimeo
Philips
IDC
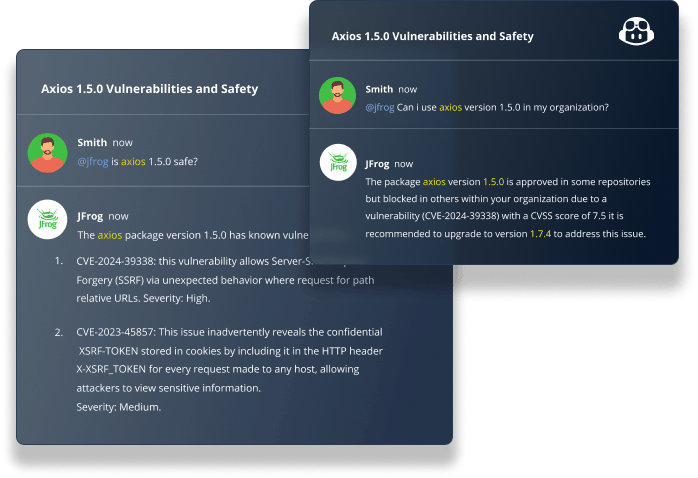
“Beyond DevOps and DevSecOps practices, the future will require advanced interactions with AI tools. Chatting with GitHub’s Copilot to select the right and secure software package based on the extensive metadata stored in JFrog Catalog can be a game-changer. This integration will significantly enhance the efficiency of Copilot users across the software supply chain; binary-focused and code environments. This partnership offers the best of both worlds."
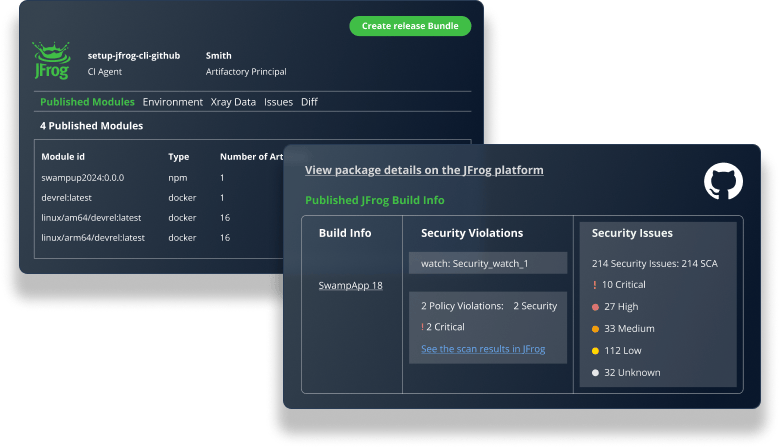
"We are thrilled to see some of the enhancements we recommended come to life; we believe this collaboration between GitHub and JFrog has the potential to significantly impact the DevOps landscape. For instance, establishing bi-directional links between GitHub Actions Workflows, Release Artifacts it created, and stored in Artifactory will enhance the development experience and traceability across the software supply chain."
"The world of software supply chain management introduces many challenges and points of friction for developers. The integration between JFrog's Software Supply Chain Platform and GitHub's Developer Platform was designed to provide a 'secure by default' developer experience. This collaboration gives developers a single source of truth for code and binaries, and security teams gain full traceability and a unified view to monitor and remediate threats, reducing risk.”
"The community and market have been anticipating this natural ‘better together’ solution. Organizations are consolidating around major best-of-breed platforms, and the partnership between GitHub and JFrog has the potential to transform the DevOps and DevSecOps market and supercharge developers’ efficiency. This integration can simplify software supply chain security by displaying source-based security findings from GitHub alongside binary-based security findings from JFrog under GitHub’s Security tab, allowing developers to gain a holistic security view and shorten remediation times to improve the overall security posture. Software supply chain security is top of mind for every CISO, and this joint solution from JFrog and GitHub provides a critical, AI-infused cybersecurity control."
"Among the strong integration capabilities between JFrog and GitHub, allowing fully-transparent and frictionless data flow between GitHub Actions/Workflows and Artifactory assets will simplify the lives of software developers, and will reduce the configuration and support load dramatically."
"As developer responsibility has increased in areas of DevOps, ML, AI, security, and more, the push by many organizations to drive efficiency via tool consolidation is a natural move,” said Jim Mercer, Program Vice President of Software Development, DevOps and DevSecOps Research at IDC. “This announcement from GitHub and JFrog helps to enable this path, bringing together two of the most well-known platforms developers already use today in a cohesive, end-to-end vision that plays to the strengths of both solutions, simplifying how development, DevOps, and platform engineering teams work."
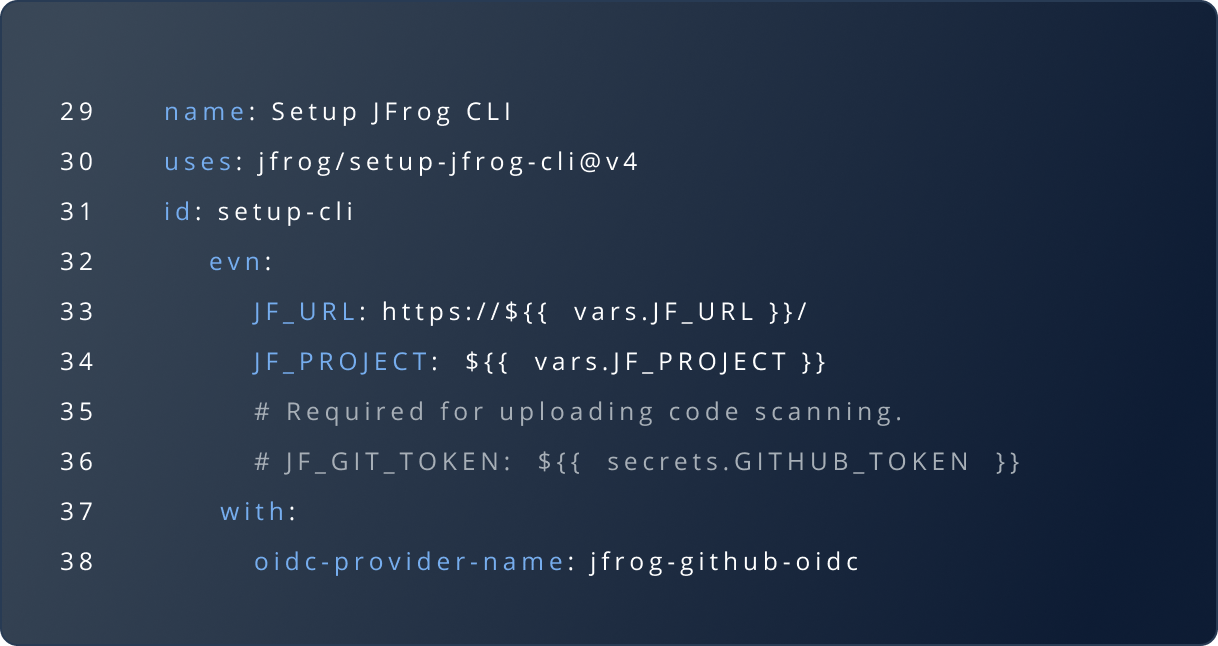
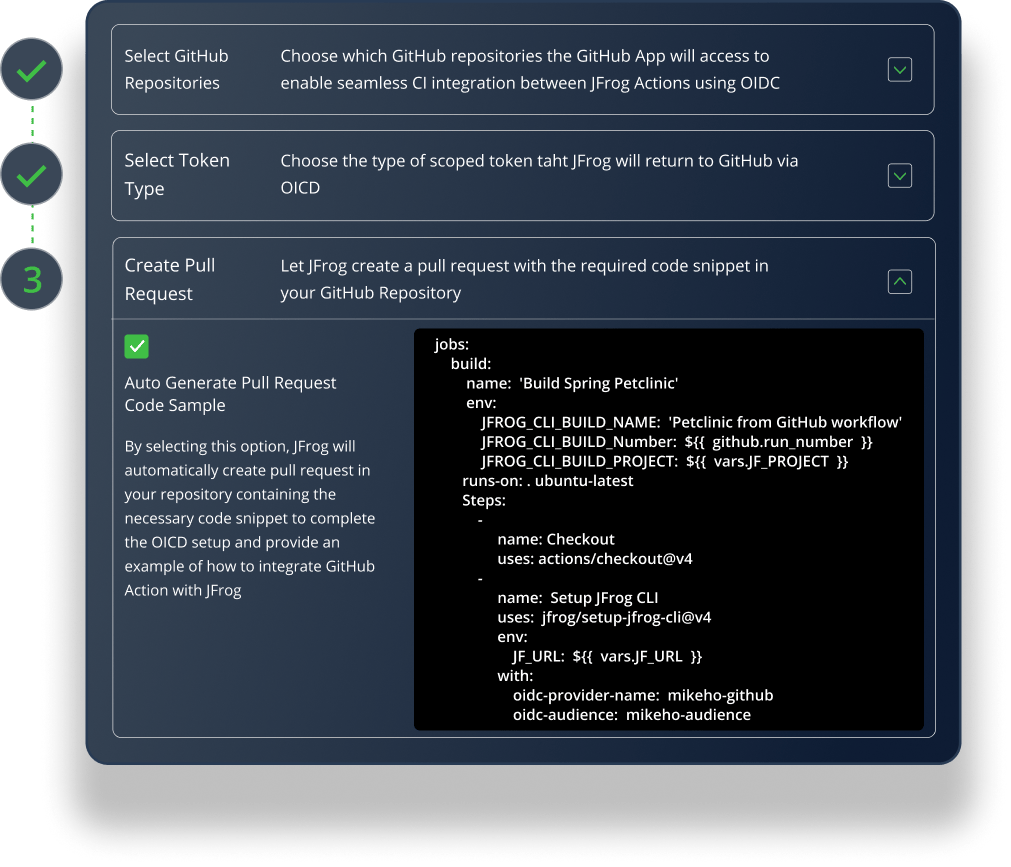
Experience the JFrog and GitHub Integration
Serving over 80% of the Fortune 100









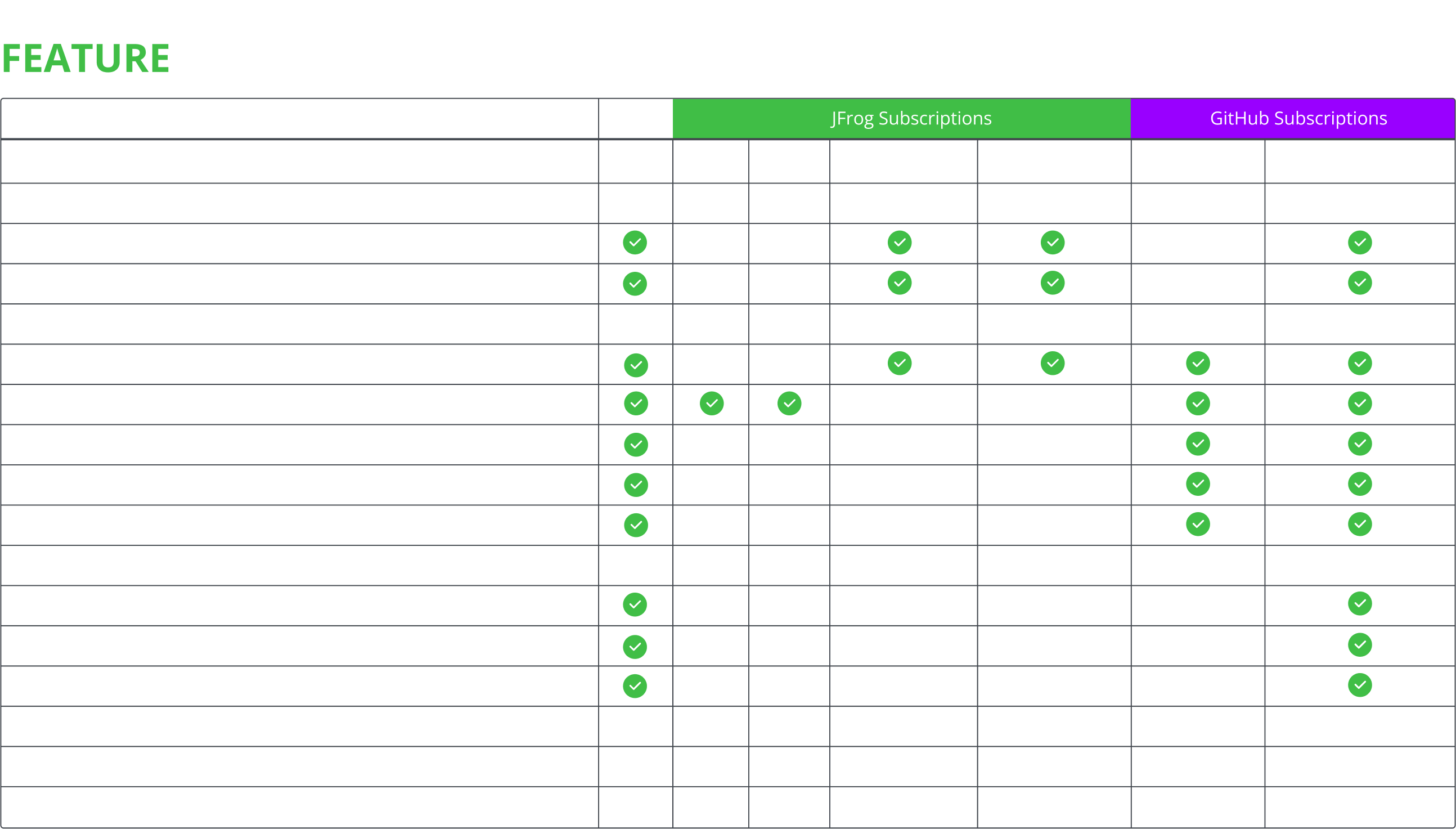
Check out all the JFrog & GitHub Integration Features