JFrog VS. Checkmarx:
AppSec Solution Comparison
JFrog takes AppSec to the next level. We don't stop at code; we proactively stop risky third-party software from ever entering your SDLC. We scan source code, binaries, containers, and runtime images, catching vulnerabilities that code-focused scanners miss. JFrog can run self-hosted, or SaaS.

By deploying JFrog, we’ve seen less vulnerabilities, which has given our developers more time to focus on developing new applications. And with the different development teams all being on the same platform, it has centralized and streamlined the process.
See how JFrog Compares to Checkmarx
Deciding between JFrog and Checkmarx?
Make the right decision. See JFrog's unique advantages.
JFrog is a holistic software supply chain security platform chosen by leading security, DevOps and development experts around the globe.
Protection beyond source code - It’s a binary difference
If you want to truly protect your applications, scanning binaries is a must. That’s why JFrog scans source AND binaries. Binaries represent the final product and its actual attack surface.
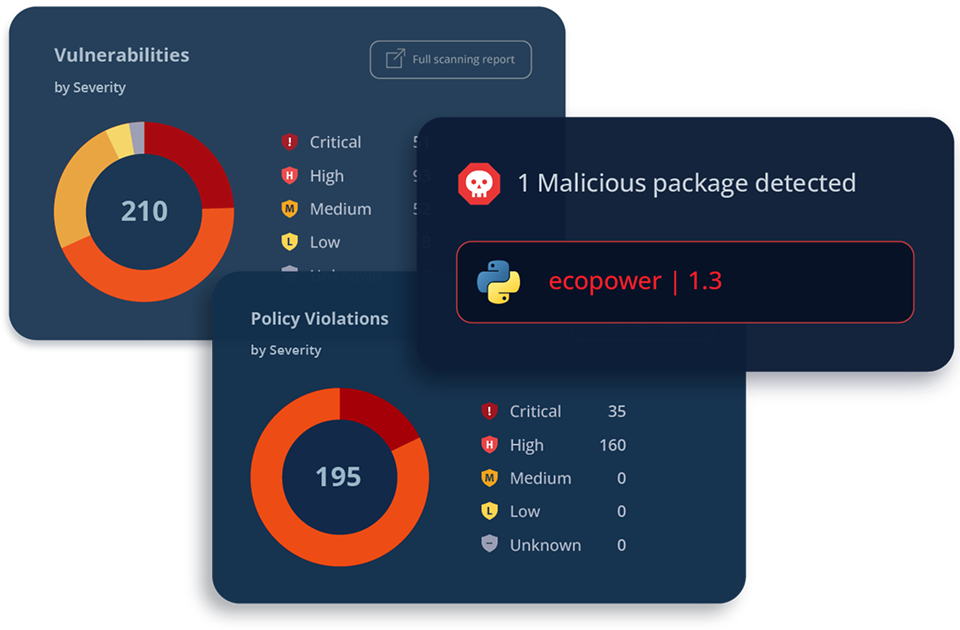
Accurate, Context-Driven Prioritization and Remediation
Limiting prioritization to code reachability, leaves you with blind spots. JFrog adds context from binaries, containers, and runtime to surface real risks and reduce false positives. Our Transitive Contextual Analysis runs deep and helps you prioritize the vulnerabilities that are actually exploitable, requiring your attention.

AppSec that is integrated in the pipelines, not bolted on
JFrog’s security solutions are an integral part of our Software Supply Chain Platform. With Artifactory acting as the single source of truth for managing all your software artifacts, models, containers, and more. JFrog’s security solutions integrate into your existing DevOps pipelines and best practices. Say goodbye to silos.

End to End AppSec, From Code to Production
Security at the gate
Block malicious or risky third party software from entering your SDLC and ensure developers are building with only vetted third-party components: Packages, models, IDE extensions and more are all curated by JFrog.
Integrated AppSec Scanners
Secure your software with JFrog’s SAST, SCA, IaC, Secrets and Runtime scanners across source and binary code. Generate SBOMs, handle configurations – All while working with developers and their tools of choice
Fix Vulnerabilities That Matter
Minimize false positives and focus on what truly matters with accurate identification of real threats: JFrog offers Transitive Contextual Analysis and prioritization of CVEs, so you can zero in on those that impact your applications.
AI/ML Security
Secure the AI you build, use AI securely. JFrog helps you with both by managing, scanning and governing your models, uncovering shadow AI, providing an AI security catalog and offering advanced AI capabilities that simplify and expedite your AppSec.
Research powered AppSec
JFrog’s Security research team is a CVE Numbering Authority (CNA). Our security products and cutting-edge innovation stem from extensive technological and community-driven research. We’re constantly on the lookout for the most recent threats and the best technological advancements to combat them.
Why Leading Companies Choose JFrog

I follow the basic principles for AppSec -- Prevent, Detect, Remediate. And when I look at the offerings from JFrog, they're checking those boxes for me.


We wanted to figure out what can we really use instead of having five, or six different applications. Is there anything we can use as a single solution? And Artifactory came to the rescue. It turned out to be a one-stop shop for us. It provided everything that we need.


By deploying JFrog, we’ve seen less vulnerabilities, which has given our developers more time to focus on developing new applications. And with the different development teams all being on the same platform, it has centralized and streamlined the process.


Since moving to Artifactory, our team has been able to cut down our maintenance burden significantly…we’re able to move on and be a more in depth DevOps organization.


Before… delivering a new AI model took weeks... Now the research team can work independently and deliver while keeping the engineering and product teams happy. We had 5 new models running in production within 4 weeks.


As our business grew, JFrog Connect helped us enhance our operations. Being able to automate and push software updates across multiple devices at once saves us time and resources with each version we deployed. When you consider the cost of an engineer’s time, it was an easy call.

-
How does JFrog compare to Checkmarx?
JFrog differs from Checkmarx in several ways. First, JFrog offers a comprehensive AppSec suite that is fully integrated with the software system of record. Checkmarx is a separate AppSec suite that requires integration with the DevOps platform. JFrog can also proactively block risky components from entering the software development lifecycle (via Curation), whereas Checkmarx is only reactive in its approach and is limited to scanning components that are already in the development environment. Finally, JFrog scans artifact binaries, which is highly effective for uncovering vulnerabilities that code scanning alone usually misses. Checkmarx’s detection capabilities are based on metadata analysis, leading to false negatives in the SBOM.
-
Can I migrate from Checkmarx to JFrog?
Migrating from Checkmarx to JFrog generally involves re-scanning software artifacts in Artifactory using Xray, which will generate a new set of security results. Users can also regenerate SBOMs for software artifacts.
-
Why choose a platform-based AppSec solution over point tools?
An integrated, platform-based AppSec approach delivers more effective security and a better DevSecOps user experience compared to managing multiple standalone security tools. Organizations using disparate point solutions often struggle with siloed toolchains, the burden of maintaining numerous platform integrations, and incomplete visibility of security issues across their software development lifecycle. By contrast, built-in security features—including SAST, software composition analysis (SCA), secrets scanning, vulnerability management, and remediation workflows—directly within your system of record provides substantial benefits. Development and security teams gain unified dashboards and streamlined processes, avoiding the inefficiency of context-switching between disconnected tools. Perhaps most crucially, this integrated platform approach provides comprehensive coverage throughout the SDLC, eliminating security blind spots that plague fragmented toolsets.
-
Does JFrog do source code scanning like Checkmarx? How do the two compare?
JFrog does source code scanning (in addition to binary scanning) as part of Xray advanced software composition analysis (SCA). JFrog Advanced Security also offers SAST, which scans source code as well.
Checkmarx needs a complete build environment to initiate a SAST scan. JFrog SAST is more efficient and runs locally on the developer’s machine, so no code leaves the developer’s environment. -
What is binary scanning and why does it matter?
Analyzing artifacts at the binary level targets vulnerabilities in the actual software components deployed to production environments. These compiled packages represent prime targets for modern threat actors who attempt to reverse-engineer them, exploit weaknesses, or distribute malicious variants—they expose details beyond what exists in the original source code. JFrog’s focus on scanning binaries is highly effective at identifying risks that otherwise remain hidden when analyzing source code alone, and delivering comprehensive insight into potential exploitation vectors and business impact. Binaries may embed sensitive elements like cryptographic keys, configuration parameters, and other data that could create security exposures for the organization.




