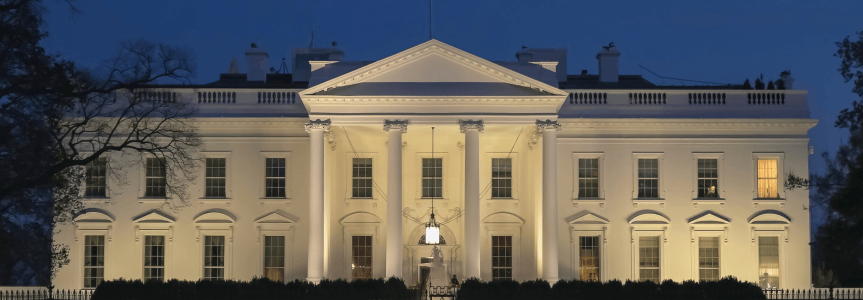
JFrog & Industry Leaders Join White House Summit on Open Source Software Security
Log4j, SpringShell and Other Zero-Day Vulnerabilities Draw Government & Tech Industry Attention
There’s no question the volume, sophistication and severity of software supply chain attacks has increased in the last year. In recent months the JFrog Security Research team tracked nearly 20 different open source software supply chain attacks – two of which were zero day threats. This steady barrage of vulnerabilities and malicious packages is driving open source leaders and the wider technology community to come together with the Biden Administration, national security organizations, and U.S. Federal agencies to devise an action plan for how to best address these attacks.
Taking place the same week as the 1-year anniversary of the Biden Administration’s Executive Order, the White House hosted part II of the Open Source Software Security Summit, May 12 – 13, 2022, with the original summit participants. A follow-up to the January 13th meeting, the event was attended by 90 executives from 37 companies – including JFrog, our partners at the Linux Foundation, and their Open Source Security Foundation (OSSF). The goal of the meeting was to identify challenges and share ideas on ways to enhance the resilience of open source software, then agree on an action plan for solidifying open source software supply chain security.
Adjusting to a New Reality
While open source has always been seen as a seed for modernization, the recent rise of software supply chain attacks has demonstrated the need for more hardened processes around validating open-source repositories. What makes open-source complicated is the fact that microservices and containers are hidden deeper within the software. All of it is designed to make development faster and more efficient, but this comes with vulnerabilities. For example, containers are great for shipping applications but, unfortunately, they’ve also made it easy to hide things.
Thus, at JFrog we believe open-source security will only be successful if we give OSS projects the same tools and services available to enterprises. Access to automated tools and high-quality security databases for open-source projects is essential and something that JFrog is committed to helping make happen.
There were two areas of discussion during last week’s OSS Security Summit that we at JFrog feel are particularly important:
- SBOMs are one of the most critical parts of providing transparency to open source supply chain vulnerabilities. The challenge today is that building an end-to-end SBOM is like precariously stacking a Jenga tower that is manually constructed and fragile to changes. To be successful, standards and tools need to be automated and combined like lego pieces in a stack so the security elements they are aiming to find can be seamlessly integrated. For example, to pull information out of builds and CI/CD systems, JFrog has open sourced Build Info which is a command line tool that automatically extracts SBOM information from the build output of a wide variety of languages and build tools. SBOMs should no longer be a nice to have, but a must have.
- Focus on enhancing the 10 most critical OSS build systems, package managers, and distribution systems with better software supply chain security tools and best practices, which will help address vulnerable software.
As a designated CNA, the JFrog Security Research team constantly monitors open-source software repositories for malicious packages that may lead to widespread software supply chain attacks and alerts the community accordingly. Thus, we know just how vulnerable software repositories can be. The hardening of existing central repositories is essential, but doesn’t go far enough to secure the software supply chain. We believe the open-source software community needs to build a decentralized package management system that only distributes binaries that were built and verified independently.
JFrog is proud to collaborate with the Linux Foundation and other OpenSSF secure software members to design a set of technologies, processes, accreditations, and policies to help protect our nation’s critical infrastructures while nurturing one of the core principles of open source software – innovation.
Last week’s summit was a notable step towards outlining an agreed-to action plan and comprehensive portfolio of 10 initiatives, which can immediately address three fundamental goals for hardening the software supply chain:
- Securing open source security production
- Improving vulnerability discovery and remediation, and
- Shortening ecosystem patching response time
We encourage you to take a look at the report and let us know your thoughts.
See what the press is saying about the White House Open Source Software Security Summit:
- “Maintainers of open source software (OSS) will gain additional security tools for their own projects, while the developers who use OSS — and about 97% of software does — will gain more data on security.” – Robert Lemos, Dark Reading
- “Securing the open-source software supply chain is a huge deal. Last year, the Biden administration issued an executive order to improve software supply chain security. This came after the Colonial Pipeline ransomware attack shut down gas and oil deliveries throughout the southeast and the SolarWinds software supply chain attack. Securing software became a top priority.” – Steven Vaughan-Nichols, ZDnet
- “Ultimately, the amount of focus on software supply chain security will advance the adoption of DevSecOps best practices…In fact, the need for more secure software is likely to accelerate the shift toward containers, since they can be ripped and replaced more easily than monolithic applications which are more challenging to patch, noted Stephen Chin.” – Mike Vizard, Security Boulevard
- “In their plan, the Linux Foundation and OpenSSF say multiple industries have identified the SBOM as a fundamental building block for solving the open-source security problem. But to suitably address the challenge, the adoption of SBOMs must be widespread, standardized and accurate. “By focusing on tools and advocacy, we can remove the barriers to generation, consumption and overall adoption of SBOMs everywhere. We can improve the security posture of the entire open-source ecosystem: producers, consumers and maintainers,” the organizations say.” – Brian Pereira, GovInfoSecurity



